Introducing the Synapse Learning Tool
by: reign | 2026-03-18
"We don’t rise to the level of our expectations; we fall to the level of our training."
~ Archilochus
Training is often the difference between individual competence and organizational excellence. It sets the standard, teaches practitioners how to meet it, and verifies their readiness to perform. Whether you're onboarding new employees or teaching advanced users a revised workflow, a well-designed training program shapes how practitioners think, teams operate, and organizations perform.
In cyber threat intelligence (CTI), the stakes can be particularly high. Intelligence assessments support decisions ranging from cyber defense and response actions to military operations. An incorrect assessment can result in reputational damage, financial loss, or even compromised individuals, data, or systems. Training ensures analysts correctly apply their domain expertise, critical thinking, and analytic rigor to complex scenarios, producing valuable intelligence.
Despite its significance, training programs often fall short due to:
Lack of standardization across teams and communities
Inability to reflect real-world scenarios
Rapid evolution of the data, tools, and methodologies
Failure to accurately measure performance
The Synapse Learning Tool addresses these challenges by enabling organizations to create, deliver, and track custom hands-on training directly within the Synapse platform. It supports training and assessment for any discipline and audience. It can be used to provide enterprise-wide cybersecurity awareness training or evaluate a developer’s coding proficiency.
In this post, we'll introduce the Learning Tool, explain how it supports training needs, highlight its core features, and walk through real-world examples that demonstrate how it can be used.
The Synapse Learning Tool
The Learning Tool is Synapse’s native Learning Management System (LMS) that enables teams to centrally create, manage, and deliver custom training and assessment content directly within the Synapse platform.
Navigating to the Synapse Learning Tool
By embedding training into the platform, users have a safe space where they can build skills using:
Real or staged data from Synapse
Actual challenges and scenarios
The actual tools and commands used in specific workflows
This approach is powerful because it allows organizations to accurately evaluate a user’s knowledge and proficiency before placing them in a live working environment.
Use Cases
Synapse's ability to accommodate multi-disciplinary data, combined with the tool's flexibility to support diverse learning assets, enables organizations to address training and assessment needs across nearly any skill, workflow, role, discipline, and industry. Here are some of the powerful ways teams can leverage the tool to develop expertise, certify proficiency, and improve performance.
Capture the Flag (CTF) Challenges
Create gamified CTF challenges with leaderboards to drive engagement and reveal top performers. Design themed events where participants solve progressive challenges and perform specific tasks within set timeframes to assess analytical skills and tradecraft.
Open-Source Intelligence (OSINT) Analysis
Provide hands-on OSINT training on extracting intelligence from open data sources. Assess learners' ability to identify valuable intelligence, create and populate nodes, link related data, and annotate nodes.
CNO Infrastructure Hunting
Train analysts to identify malicious infrastructure using network data such as passive DNS, WHOIS records, TLS certificates, ASN data, and server scans. Assess their ability to hunt for CNO infrastructure, codify adversary TTPs, and correlate activity.
Financial Crime Analysis
Present learners with financial data to identify fraudulent patterns. Assess their ability to follow the money, detect fraud, and uncover money laundering activity.
Compliance and Corporate Training
Deliver and track mandatory training on security policies, data handling procedures, or regulatory requirements. Verify understanding through quizzes that require passing scores.
Core Components and Features
The Learning Tool allows you to create structured, customizable learning experiences. In this section we’ll highlight the core components and features that support content creation and delivery.
Content Creation and Management
Effective training starts with the ability to develop content tailored to your specific learning needs. The tool incorporates several components to make this possible.
Learning Asset Manager with WYSIWYG (What-You-See-Is-What-You-Get) drag-and-drop interface for creating, organizing, and managing learning assets and their associated permissions
Courses and Modules for organizing learning assets and scaffolding learning
Rich content formats including text, images, video, audio, and executable code blocks can be combined using the embedded rich text editor
Real data integration from an associated Synapse view
Assessment and Tracking
Learning Tool Dashboard for personalized progress tracking
Quizzes to assess learners using various question formats and auto-grading
Forked Views for hands-on practice without production impact
Storm Callbacks to automate post quiz actions including permission assignment
Gamification
Events to time-bound challenges
Challenge Leaderboard for real-time visibility and creating competition
The Learning Tool in Action
The most effective way to understand the Learning Tool's features and capabilities is to see it in action. To do that, let's walk through three examples we've created:
Storm 101- A self-paced training courseSleuthCon 2025- A competitive CTF-style account takeover (ATO) and fraud investigationPIVOTCon 2025- A reflective threat clustering workshop
Together, they highlight the diverse training and assessment experiences you can create and demonstrate how it can accommodate your training needs.
Storm 101: Query Language Fundamentals
What We Built
We created this self-paced course to teach users the basics of the Storm query language and evaluate their ability to construct Storm queries used in common CTI analysis workflows. We use this training to ensure that users are proficient in Storm before granting them tagging permissions in our production environment.
Storm 101: Query Language Fundamentals
How We Built It
We created a hands-on course covering basic Storm query concepts through scaffolding modules. We combined real-world threat data with both static and interactive content to demonstrate Storm operations and let students practice query execution inline with module content. Each module ends with a quiz, and the course ends with a final assessment to evaluate their overall Storm knowledge and proficiency.
We built this using the following components:
Courses and Modules - We divided the content into manageable sections sequenced in a natural progression, helping learners easily progress from basic concepts to practical application.
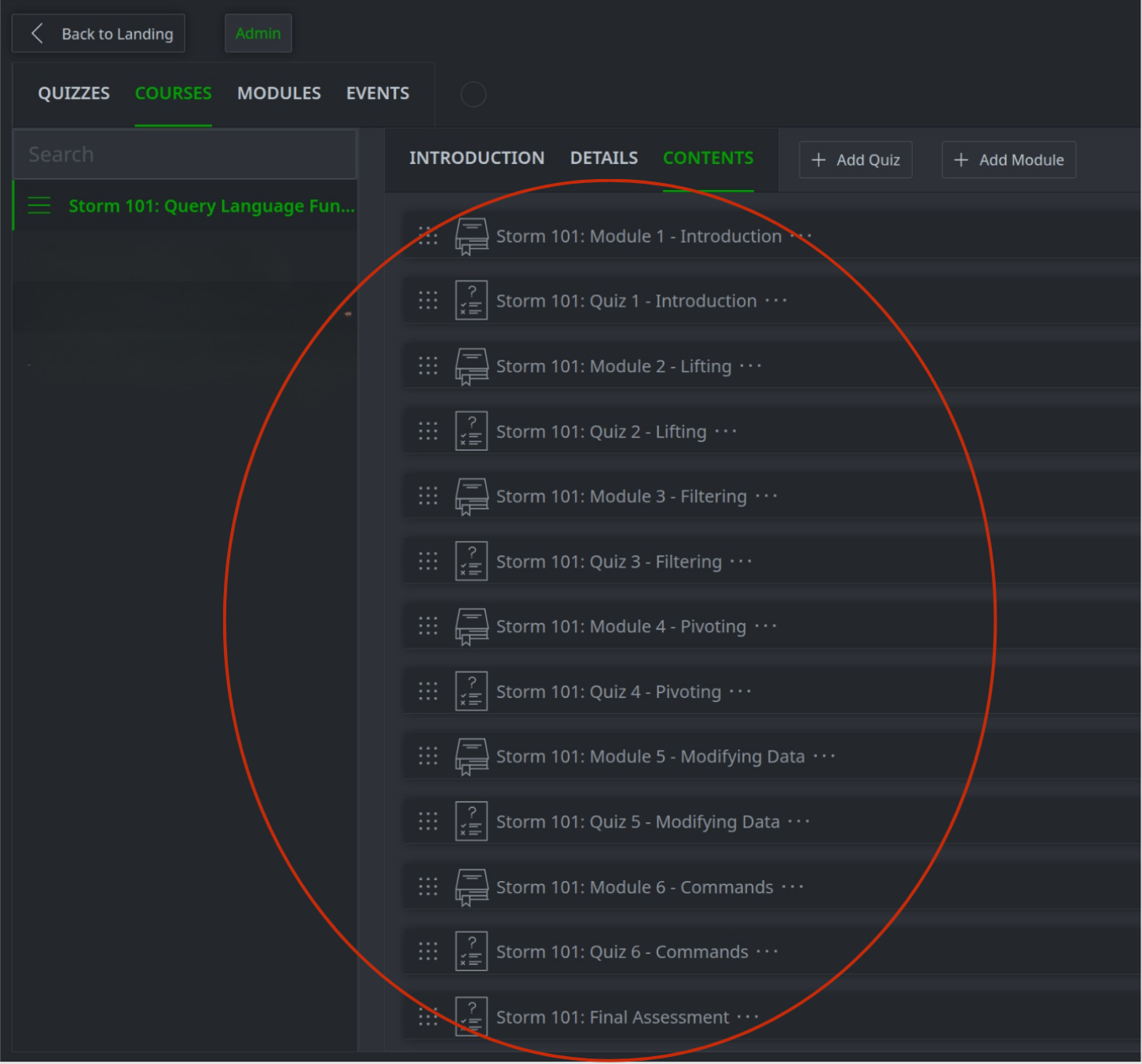
Storm 101 modules and quizzes
Code blocks - We leveraged the code block feature to let students run Storm code inline without manually writing queries, which is important when transitioning learning from concept to application.
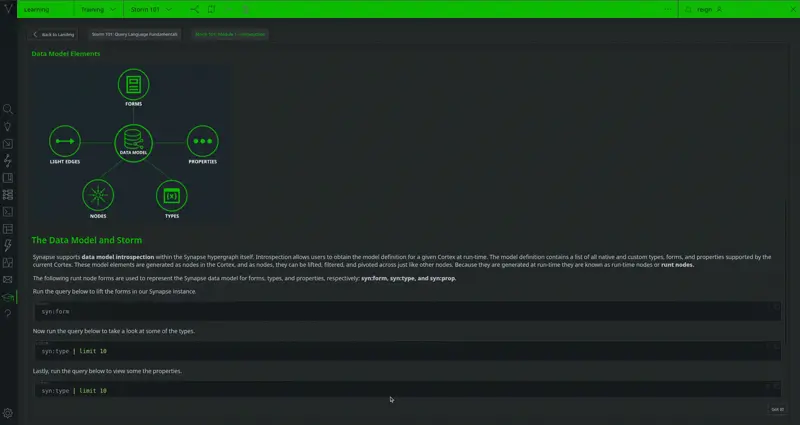
Storm code block example
Quizzes - We added quizzes at the end of each module to reinforce learning and a final assessment to evaluate overall performance. Questions mixed multiple-choice and hands-on tasks to assess both conceptual knowledge and practical skills like lifting, exploring, and tagging nodes.
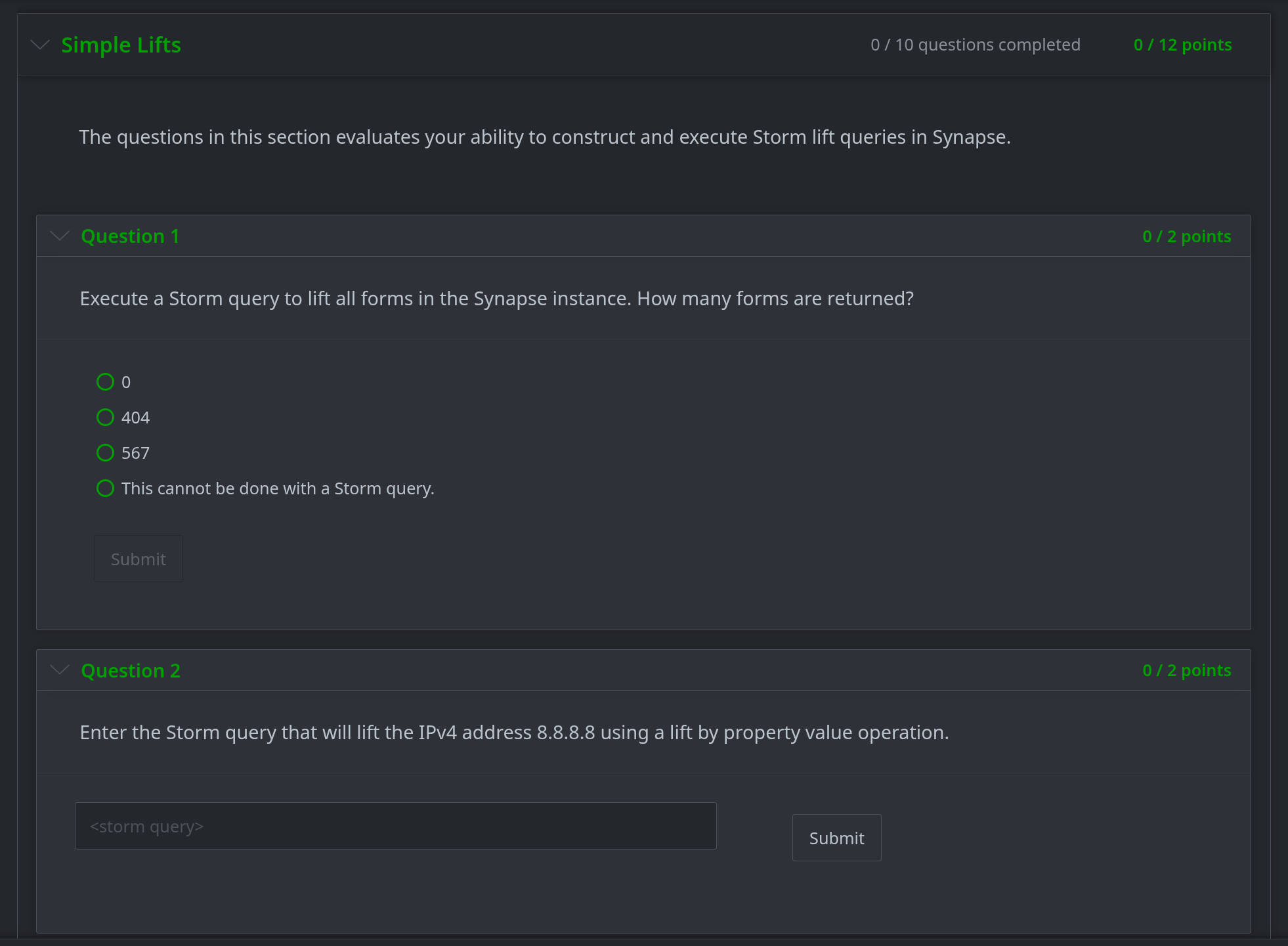
Storm 101 quiz questions
Views - We populated a view with real CTI threat and enrichment data, allowing users to learn with actual data and be evaluated on constructing queries that align with real analysis workflows.
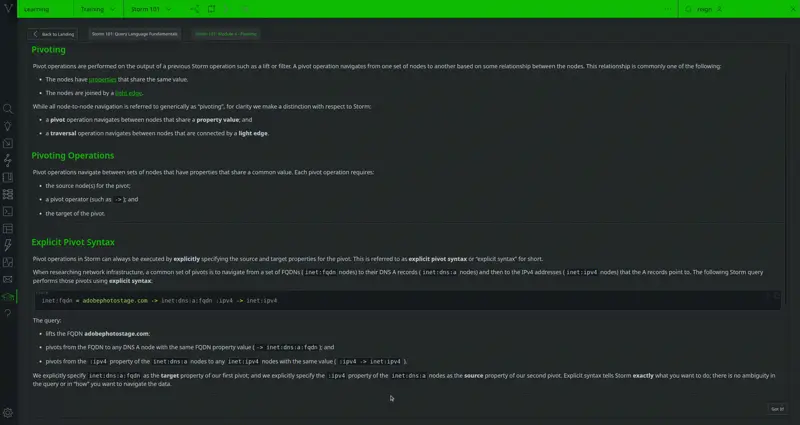
Storm 101 module content and query data
Storm Callbacks - These are saved Storm queries that run when a specific condition is met. We used these to automatically grant tag permissions to trainees who scored 80% or above, allowing them to immediately annotate data in the system.
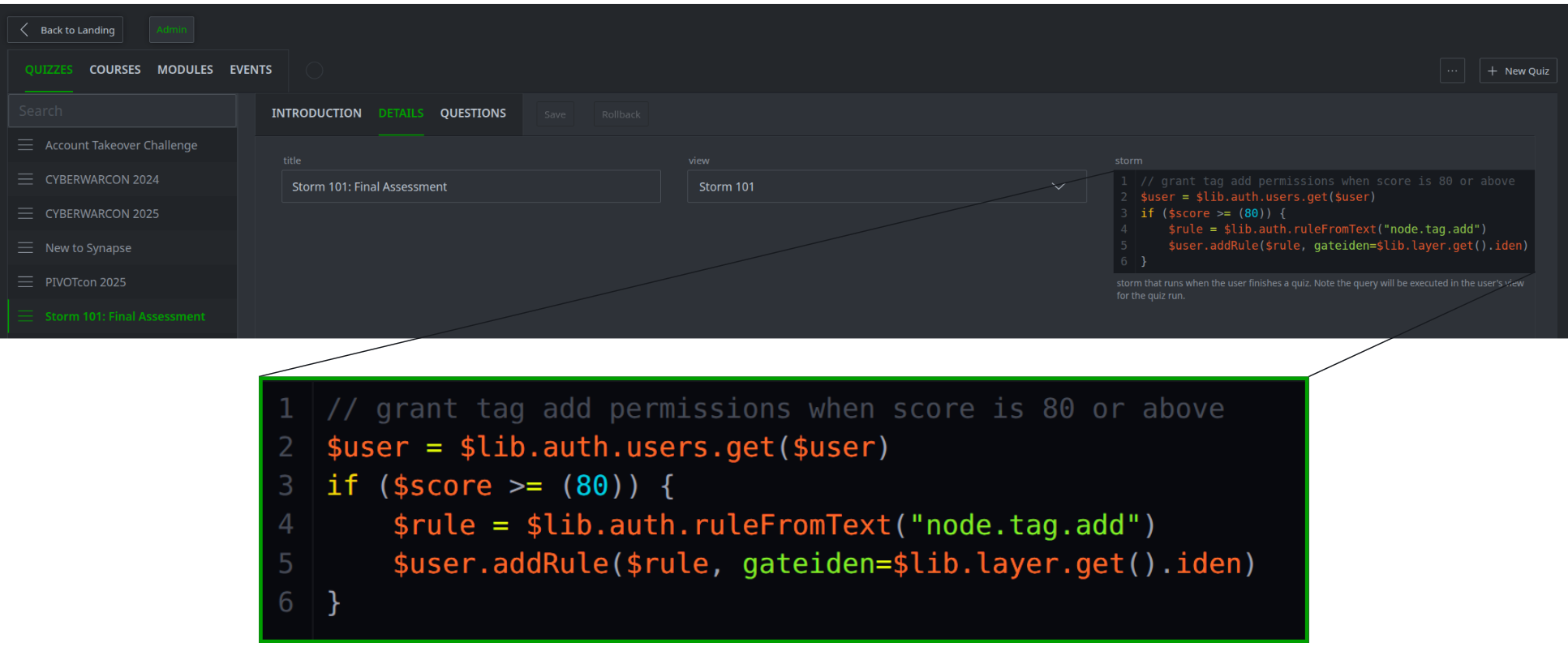
Storm callback code for granting tag add permissions
The Outcome
This approach helps us verify user Storm proficiency at scale. Hands-on assessments and automated permission checks ensure that only qualified users gain access to production systems, without manual review. This approach speeds up analyst onboarding, maintains quality standards, and allows the course to evolve as Storm capabilities expand.
SLEUTHCON 2025: Account Takeover Investigation
What We Built
We created this competitive Synapse challenge for SLEUTHCON 2025. The challenge uses an account takeover (ATO) and fraud scenario to evaluate participants' ability to provide cyber threat intelligence support for a potential ATO and payment fraud investigation in a fast-paced environment. Participants must collaborate with internal teams to rapidly analyze actor activity, and correlate cyber threat activity with online banking transactions to confirm fraud.
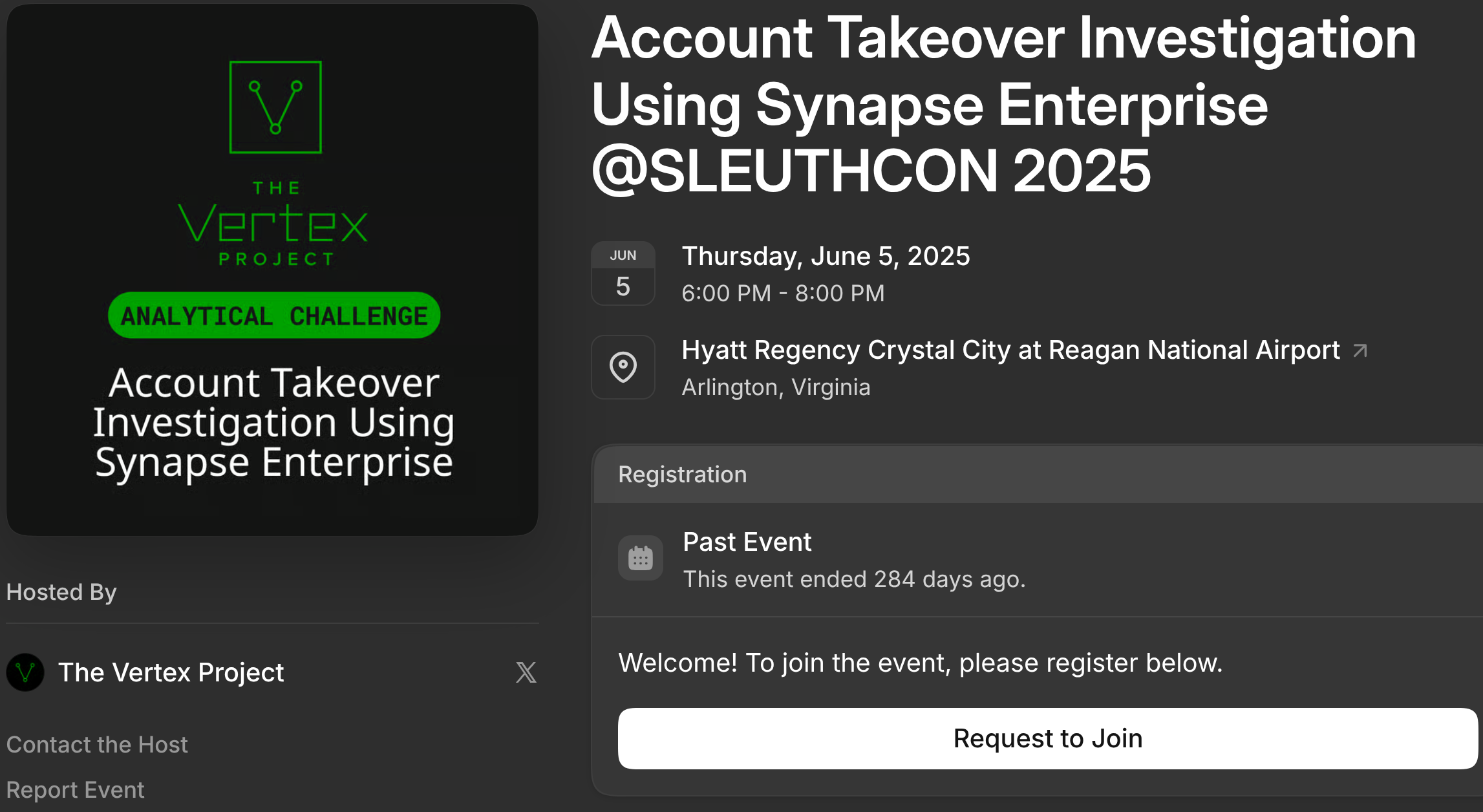
SLEUTHCON 2025 Synapse Challenge registration page
How We Built It
This challenge used the Learning Tool to deliver an interactive and competitive ATO and fraud investigation. We used realistic intrusion data, a time-bound Event with a leaderboard, and task-based quiz questions to simulate a time-sensitive security incident. Participants work through increasingly complex investigative tasks while the platform tracks their performance in real-time.

SLEUTHCON 2025 Synapse Challenge
SLEUTHCON 2025 Synapse Challenge mission
We built this using the following components:
Events - We used this feature to create a friendly yet competitive, time-bound challenge with a live Challenge Leaderboard. This allowed us to turn a simple investigation into an engaging competition that rewards accuracy and speed.
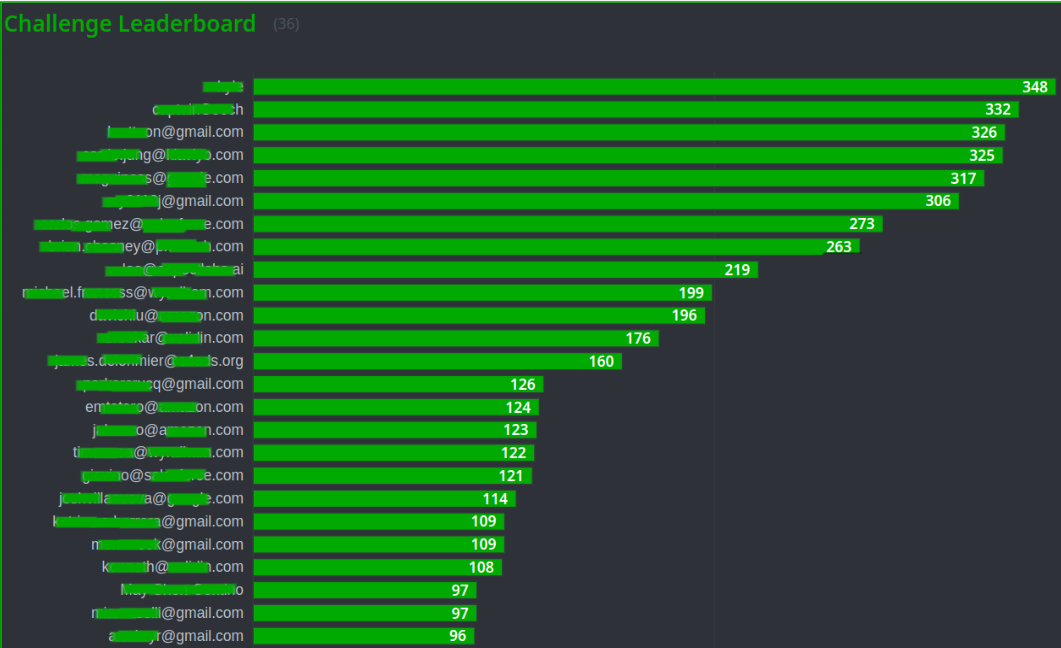
SLEUTHCON 2025 Synapse Challenge Leaderboard
Quizzes - We used a quiz to create a scenario-driven investigation where questions are framed as investigative tasks that increase in complexity to mirror real fraud analysis workflows. The Hints feature guided participants when needed and configured retry penalties to discourage guessing.
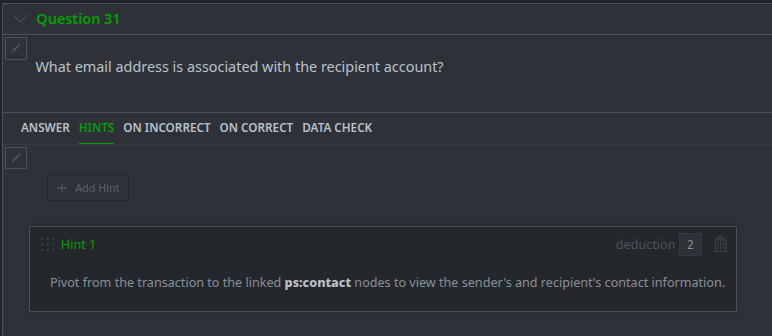
SLEUTHCON 2025 Synapse Challenge question hint
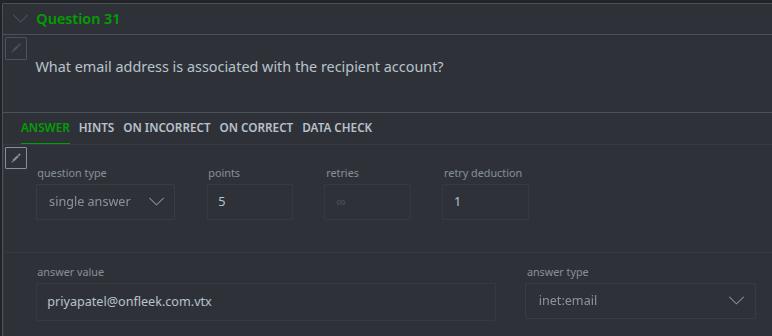
SLEUTHCON 2025 Synapse Challenge question retry point deduction
Views - This challenge used a dedicated view with fabricated ATO and payment fraud data including login events, phishing and smishing messages, payment transactions, and network and infrastructure data.
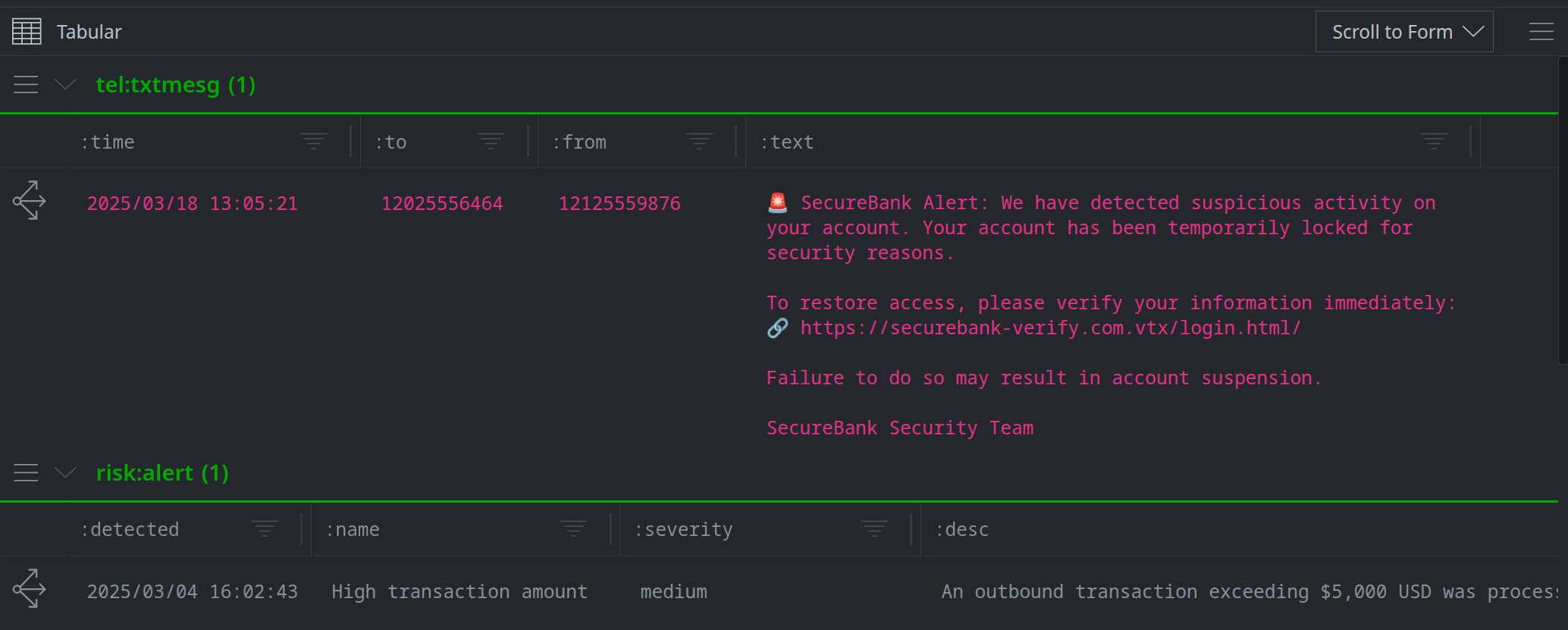
SLEUTHCON 2025 Synapse Challenge view data
The Outcome
Using the Learning Tool we were able to simulate a time-sensitive fraud investigation that assessed cyber threat intelligence support skills. The Challenge Leaderboard and cross-functional scenario gave analysts experience with a fast-paced investigation in a safe environment.
PIVOTCon 2025: Threat Clustering Workshop
What We Built
We developed this challenge for a PIVOTcon 2025 threat clustering workshop. Unlike SLEUTHCON's competitive investigation, this challenge prompts analysts to examine and reflect on threat intelligence clustering and public CTI reporting tradecraft. This workshop highlights the methodological challenges facing the CTI community and encourages discussion about improving clustering practices, attribution decisions, and intelligence sharing.
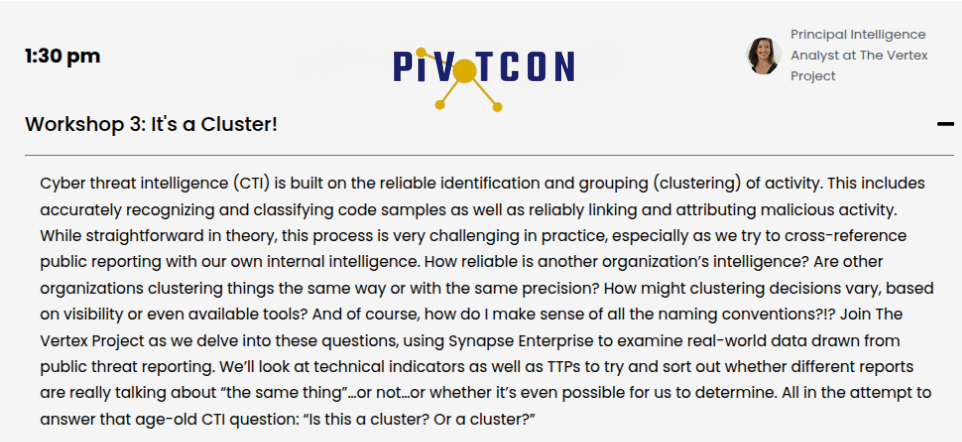
PIVOTCon 2025 Workshop
How We Built It
We used the Learning Tool to create an interactive workshop that uses real threat data and CTI OSINT reports to guide participants through clustering threat activity and evaluating third-party reports. We combined Synapse tools like Spotlight and the Threat Intel Workflow with the tool's integrated feedback features to prompt critical reflection on analytical tradecraft used and observed throughout the challenge.
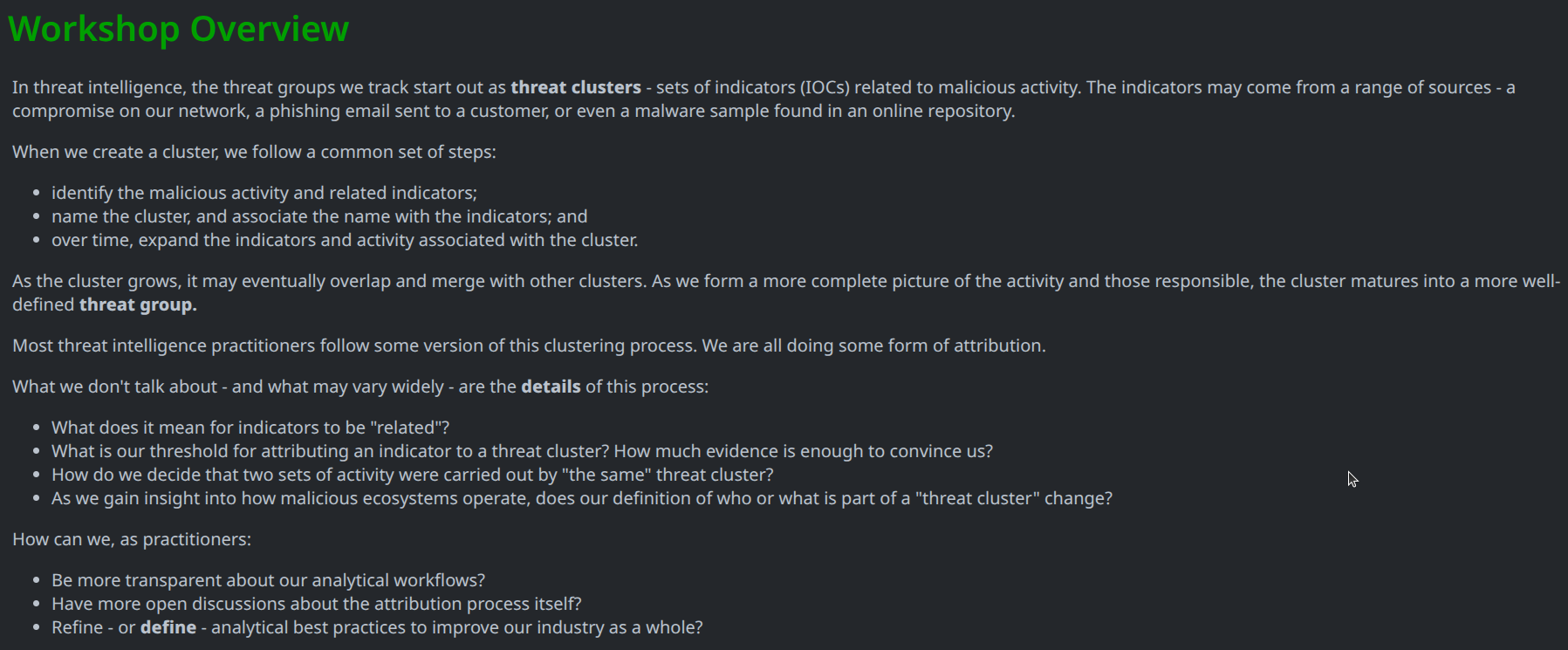
PIVOTCon 2025 Workshop overview
We built this using the following components:
Events - Like SLEUTHCON 2025, this was also a time-bound challenge with a Challenge Leaderboard. However, here the leaderboard fostered engagement rather than speed, as the goal was to encourage critical thinking and reflection.
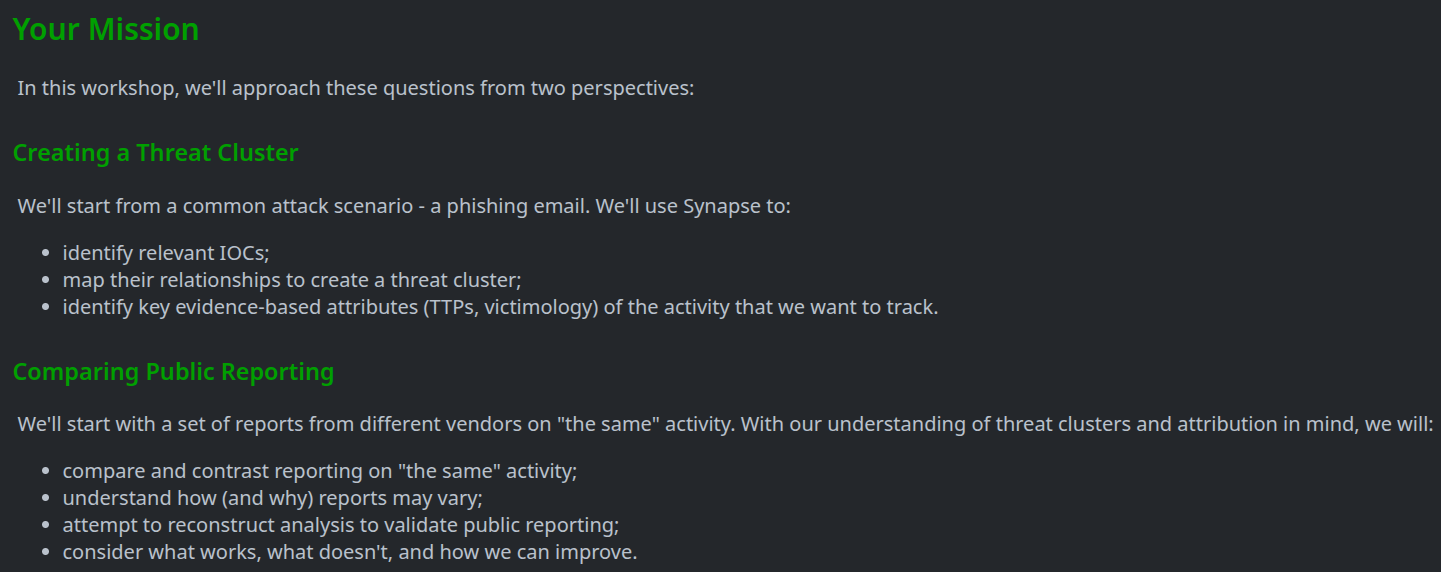
PIVOTCon 2025 Workshop mission
Quizzes - We used this feature to guide users during clustering tasks and public report analysis. The ability to pair visuals with narratives made it easy to insert reflective checkpoints and review analytical tradecraft.
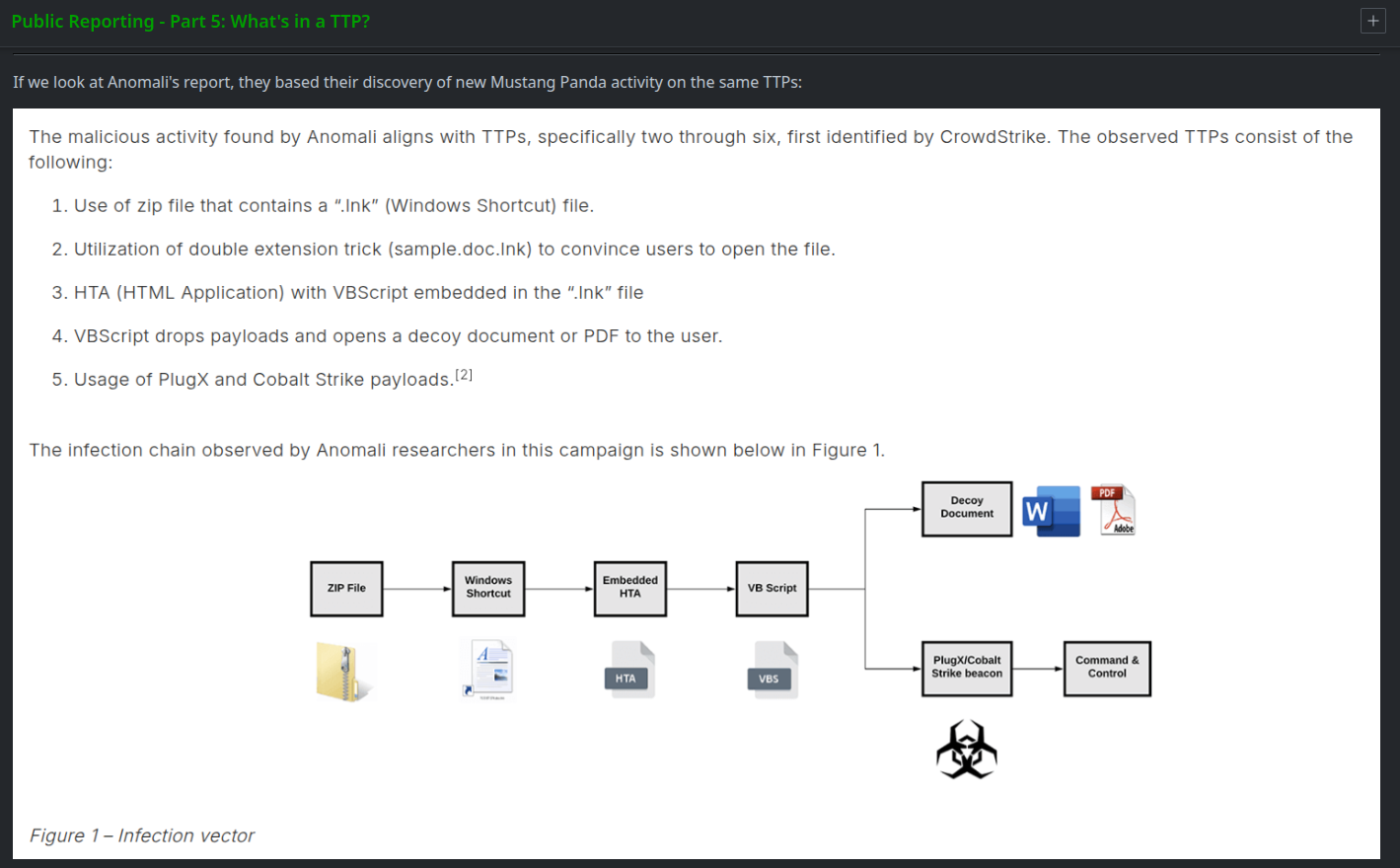
PIVOTCon 2025 Workshop quiz section with embedded image
PIVOTCon 2025 Workshop question referencing an embedded image
Correct/Incorrect Feedback - We used the On Incorrect and On Correct quiz features to guide participants when they submitted wrong answers and offer supplemental context for correct ones.
Views - We populated the workshop's view with real host-based and network artifacts including phishing emails, malware execution data, MITRE ATT&CK TTPs, and public reports, giving participants a comprehensive data set for threat clustering analysis.
The Outcome
The Learning Tool allowed us to deliver a workshop that fostered critical thinking and tradecraft review, not just competition. By pairing challenge tasks with methodology-specific feedback, we were able to challenge analytical assumptions, highlight gaps in CTI community practices, and encourage discussion about threat intelligence standards.
What This Shows
These three training use cases demonstrate how the Learning Tool supports diverse training needs and the power of embedding training in your operational environment. Whether certifying Storm proficiency, evaluating fraud analysis skills, or examining clustering methodology, each use case leveraged the same core capability: hands-on learning with real Synapse data and operational tools.
Getting Started
The Synapse Learning Tool delivers hands-on training directly within the analysis environment, helping organizations overcome common gaps in traditional programs. By embedding learning into real workflows and using actual data and tools, it ensures training reflects real-world scenarios, supports standardization, and accurately measures performance.
Whether through self-paced courses, time-bound investigative challenges, or reflective workshops, the platform enables teams to build practical skills, verify proficiency before production access, and adapt content for any discipline or skill level. With gamification features like timed events and leaderboards, it also keeps learners engaged and motivated.
Try the Threat Clustering Challenge!
We’ve added the PIVOTCon 2025 threat clustering challenge to the Vertex Intel Sharing Instance. This challenge is a great way to explore the Learning Tool and also put your threat clustering skills to the test. Instructions for accessing the challenge can be found in our Threat Clustering Challenge blog.
