Top Lessons from Operation Deepfake & What They Teach Us About Insider Risks
the vertex project | 2026-01-29
In October 2025, The Vertex Project hosted a Synapse investigation centered around an insider threat incident. This challenge, titled Operation Deepfake, is now available in the Vertex Intel-Sharing Synapse Instance (VISI) for analysts to try. While our prior challenges tend to focus more heavily on technical investigations, Operation Deepfake highlights some of the contextual complexities inherent to insider threat investigations. These include identifying whether the threat is internal or external to the organization, and whether an incident is the result of malicious activity, negligence, competing priorities, simple technical or human error, or a combination of all of the above. Operation Deepfake incorporates these various elements to challenge how analysts think, rather than just what they know. In this blog, we’ll highlight some of the key lessons from Operation Deepfake and what they can teach us about insider threat risks.
Synapse investigative challenge Operation Deepfake is now available on the VISI for analysts to try
Lesson #1: Collaboration is a Must
Operation Deepfake is our most expansive Synapse challenge to date, mirroring how effective insider threat investigation and response requires collaboration across multiple sections of an organization. Insider incidents rarely sit cleanly within one department, and the incident in this challenge is no different. To track the activity, participants must collaborate with employees working within information technology, product development, and human resources, among other departments. Each department has its own crucial visibility into the incident, and sharing information and findings across teams accelerates the investigation.
Without this collaboration, our participants would be faced with the same data silos that analysts dread. The ability to collaborate and incorporate findings from multiple sources is intrinsic to Synapse, which is a centralized intelligence system in which users can work together to analyze data from disparate sources and share findings. While it is certainly possible to operate independently and contend with data silos, the ability to share insights and information when desired is key for an efficient and effective investigation and response.
The challenge will prompt analysts to work with employees and data across the victim organization to complete the investigation
Lesson #2: Context is Key
No single glaring red flag in Operation Deepfake indicates malicious activity. Since insider threats are as much human as technical, much of the challenge for Operation Deepfake participants involves analyzing employee behavior and patterns, rather than looking for a technical indicator like a command and control beacon or a suspicious download. Context is key in this scenario, and participants must take a holistic view of the data, as many of the individual data points are benign when reviewed in isolation.
Analysts will examine a range of information to identify additional investigative paths
Synapse is designed for this kind of relationship-driven analysis, allowing analysts to identify and track contextual clues to make sense of data and reason through ambiguity. Participants will need to use Synapse to consider multiple factors such as timing, access, roles, and patterns of behavior when analyzing activity to determine whether or not it is suspicious. With this holistic view of the data, participants can identify patterns of behavior that - when viewed in context - no longer appear benign but as actions worthy of further investigation.
Lesson #3: Uncertainty is Part of the Job
Just as in an actual investigation, Operation Deepfake participants must contend with incomplete data and conflicting interpretations, all while operating under a time crunch. This forces analysts to prioritize their efforts and make the best judgments they can with the information available. Crucially, analysts must also be able to update their assessments as additional, potentially conflicting, data comes to light.
Analysts working in Synapse are encouraged to show their work and model supporting evidence behind their assessments. This not only allows for analytical transparency, but can be particularly helpful if new information later renders that assessment inaccurate. In such a case, the analyst can identify where their findings diverged and update their assessment with the current evidence.
Incomplete and conflicting data requires analysts to use their best judgment with the information at hand
Lesson #4: Tools Don't Solve Problems - Analysts Do
This challenge emphasizes the importance of analysts, rather than tools, when it comes to identifying and investigating security breaches. Insider threat activity can be subtle, making effective detection reliant upon contextual clues and human assessment. The nature of the activity - in which individual data points appear benign - is well-suited to analytic reasoning. Good tools like Synapse can help analysts view and interrogate data, make connections, and share findings, but are no replacement for analysts themselves.
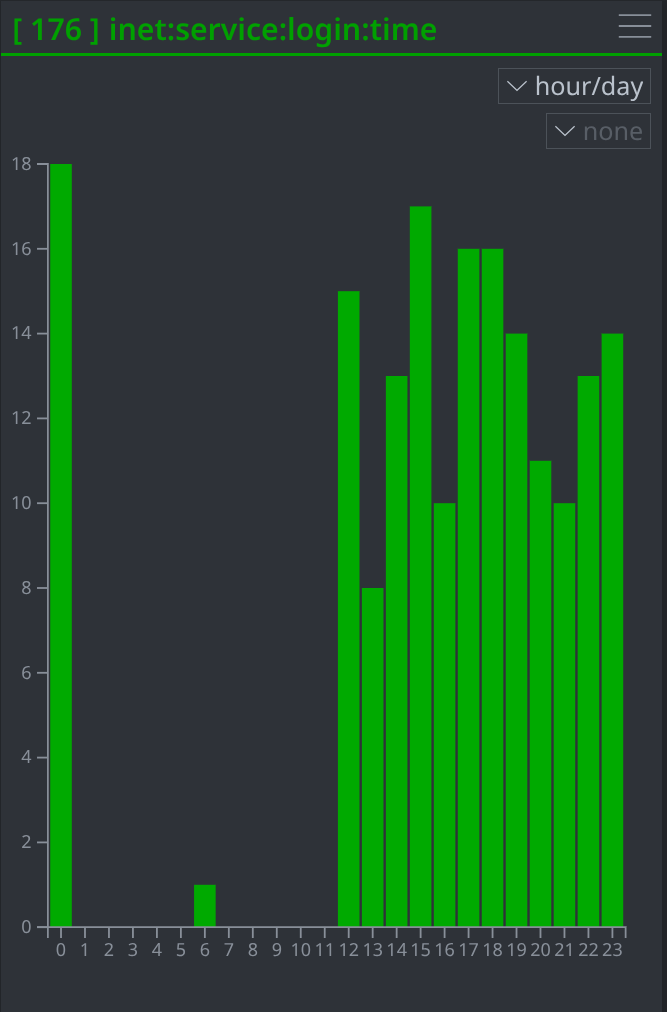
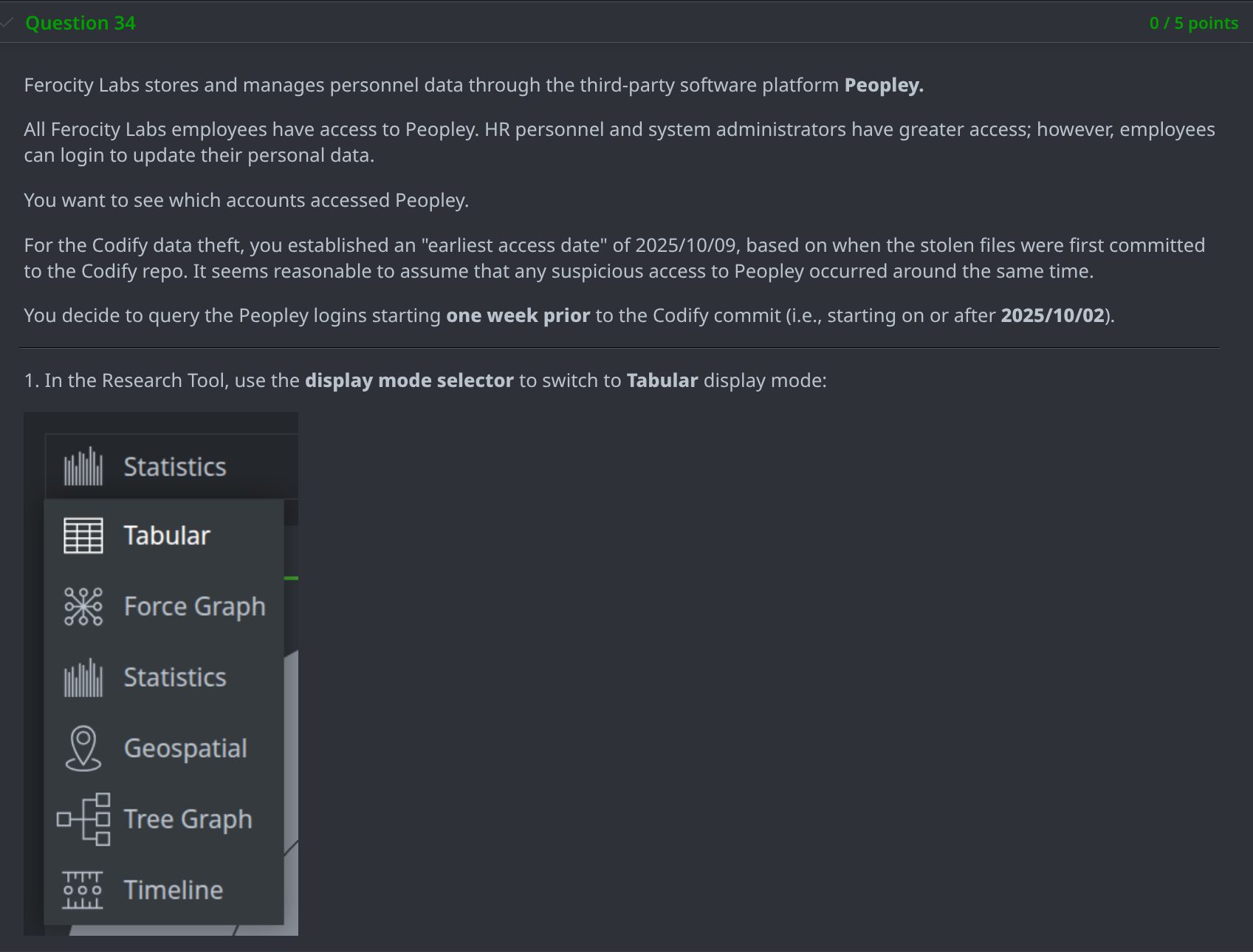
Tools can help analysts visualize data, like login times
Why We Built Operation Deepfake
We developed Operation Deepfake with the intent to create an investigative challenge that explores how analysts approach complex problems. There is a growing awareness of the risk posed by insider threats, particularly from state-sponsored operations seeking to place insiders in targeted companies. However, as is often the case, analysis experience and training lags behind this threat. This scenario is designed to be a realistic, thought-provoking exercise where analysts can practice making hard decisions in a low-risk environment.
Try the Challenge for Yourself
Ready to test your analytic skills against an insider threat? Operation Deepfake is available for users to try at their own pace on the Vertex Intel-Sharing Synapse Instance - a community Synapse instance hosted by The Vertex Project. This challenge is appropriate for both new and experienced Synapse users, as well as for analysts in both technical and non-technical roles.
Find Operation Deepfake in the Vertex Intel-Sharing Synapse Instance (VISI)
To learn more about Synapse, join our Slack community, check out our videos on Youtube, and follow us on Bluesky (or on X).
