Cloud Threat Intelligence in Synapse
by: reign | 2026-04-30
"The whole is greater than the sum of its parts." ~ Aristotle
Cyber threat intelligence (CTI) analysis has traditionally relied on technical observables like IP addresses, domain names, TLS certificates, and DNS records to identify and track threat activity and attacker infrastructure. However, as both enterprises and threat actors shift to cloud environments, traditional observables no longer reflect the full scope of modern threat activity.
Platforms such as Microsoft Azure, Google Cloud, Amazon Web Services (AWS), GitHub, and Dropbox now underpin both legitimate business operations and computer network operations (CNO). Threat actors exploit these same trusted platforms to conduct everything from initial reconnaissance to command and control (C2), blending in with normal traffic to evade detection, establish persistence, and operate at scale.
This shift introduces a new class of observables alongside traditional indicators, including cloud accounts, API endpoints, OAuth tokens, storage buckets, repositories, and serverless functions. Despite their pervasiveness, these artifacts aren’t represented as first-class entities in existing CTI workflows, creating gaps in our understanding of actor infrastructure, tradecraft, and victimology, and limiting our ability to support effective detection and response. As a result, CTI workflows must evolve to incorporate, track, and correlate cloud threat data.
In this blog, we draw on real-world threat activity to demonstrate how Synapse's expanded data model enables analysts to modernize their workflows and analyze cloud-based threat activity with the same rigor applied to traditional infrastructure. This post builds on, Modeling Platforms, Accounts, Messages, and More with the inet:service:* Forms, which introduced the core inet:service:* data model elements used to represent cloud-based activity.
The Rise of Legitimate Infrastructure in Threat Activity
The use of legitimate services in computer network operations is not new, but its scale and prevalence have made it the norm. As early as 2014, FireEye observed the Chinese threat actor APT17 leverage Microsoft TechNet as a dead drop resolver by embedding encoded BLACKCOFFEE malware C2 IP addresses into user profiles or forum threads.
At the time, this technique was novel. Today, threat actors abuse every type of cloud service for operations:
Infrastructure as a Service (IaaS): Managed computing resources (e.g., AWS EC2, Azure VMs).
Platform as a Service (PaaS): A managed environment for building and running applications (e.g., Azure App Service, Heroku).
Software as a Service (SaaS): Managed applications accessed over the Internet (e.g., GitHub, Dropbox).
Function as a Service (FaaS): Event-driven execution of serverless functions (e.g., AWS Lambda, Google Cloud Functions).
From Novelty to the New Normal
Cloud services offer threat actors trusted infrastructure, global scale, rapid provisioning, and built-in anonymity, oftentimes for free, making them an invaluable resource for every stage of the Targeted Attack Lifecycle. The table below documents publicly reported cloud service abuse across each phase, highlighting its widespread use.
Targeted Attack Lifecycle Phase |
Threat Group |
Cloud Service |
Activity |
|---|---|---|---|
Initial reconnaissance |
Peach Sandstorm (Microsoft) |
Peach Sandstorm used fake LinkedIn accounts to conduct information gathering on targets and communities of interest. [1] |
|
Initial compromise |
PINEAPPLE (Google) |
Google Cloud Run |
PINEAPPLE created malicious container-hosted URLs on legitimate Google domains to distribute malware. [2] |
Establish foothold |
Midnight Blizzard (Microsoft) |
Microsoft Entra ID |
Midnight Blizzard created malicious OAuth applications to establish a foothold in the target environment. [3] |
Escalate privileges |
UNC3944 (Google) |
Okta |
UNC3944 abused Okta permissions to escalate privileges and expand access across cloud and SaaS environments. [4] |
Internal reconnaissance |
Storm-0501 (Microsoft) |
Microsoft Azure |
Storm-0501 used a privileged account to execute AzureHound and enumerate users, roles, and Azure resources within a compromised tenant. [5] |
Move laterally |
UNC3944 (Google) |
Microsoft Azure |
UNC3944 used the Azure Serial Console to move laterally to virtual machines in a target's Azure environment. [6] |
Maintain presence |
Peach Sandstorm (Microsoft) |
Microsoft Azure |
Peach Sandstorm created Microsoft tenants to maintain persistent access to target environments. [7] |
Command and control |
OilRig (ESET) |
Microsoft OneDrive |
OilRig downloaders leveraged OneDrive for C2. [8] |
Completing mission |
Crimson Collective (Rapid7) |
AWS RDS, EBS, EC2 |
Crimson Collective stored RDS and EBS backups in S3, and exfiltrated the data via attacker-controlled EC2 instances. [9] |
These examples indicate that cloud abuse is no longer novel or an emerging trend, but a standard component of modern threat activity. Threat actors across every geographic region, sophistication level, and operational goal are systematically incorporating cloud platforms into their operations. To keep pace, CTI telemetry, data models, and workflows must evolve to incorporate cloud threat data.
Evolving CTI Analysis for Cloud-Based Threat Activity
Traditional CTI infrastructure analysis centers on technical observables like IP addresses, domain names, ASNs, DNS records, TLS certificates, and WHOIS data. While these are still relevant, they now appear alongside cloud-based artifacts. In cloud-enabled operations, accounts are replacing dedicated servers, storage URLs are replacing actor-registered domains, API keys are replacing passwords, and code repositories are replacing actor-controlled servers for staging.
As shown below, this shifts the data analysts need to collect, how they cluster, correlate, and attribute threat activity, and how they detect and respond to threats.
Analysis Component |
Traditional CTI |
Cloud-Based CTI |
|---|---|---|
Data Sources |
On-premise firewall and network logs, sandbox execution data, active and passive DNS DBs, WHOIS DBs, ASN and geolocation DBs, sinkholes, certificate transparency logs |
Cloud service API and activity logs (e.g., CloudTrail), public APIs, platform-specific account and profile data, sandbox API data (e.g., VirusTotal Comments API) |
Indicators |
IP addresses, FQDNs, URLs, email header data, SSL certificates, JARM hashes |
API endpoint URLs, account profile data and metadata, messages, comments, code repositories and commits |
Correlation |
IP/FQDN/URL overlaps, DNS resolution data, nameservers, TLS certificate reuse |
Artifact reuse across operations, cross-platform account similarities, dead drop resolver C2 config the overlaps, artifact timestamp proximity |
Clustering and Attribution |
WHOIS records, ASN use, domain registrars, hosting providers, domain naming conventions, certificate authority providers, malware traffic patterns, operational times |
Artifact reuse across malware and campaigns, platform-specific abuse patterns, platform usage sequence |
Detection |
IP blocklists, certificate revocation list, DGA detection, protocol anomaly detection |
API usage anomaly detection, platform data transfer volume |
Cloud threat intelligence extends traditional CTI analysis rather than replacing it. Both must be used in parallel to fully understand and characterize modern threat activity.
Modeling Cloud Threats in Synapse
To effectively analyze cloud threat activity, analysts need the ability to model both abstract and concrete cloud data such as identities, infrastructure, services, and resources, alongside CNO risks, threats, and TTPs.
The table below maps commonly targeted and abused cloud components to the Synapse forms we use to represent them:
Cloud Service Targets |
Synapse Form |
|---|---|
Platforms |
inet:service:platform |
Managed applications |
inet:service:platform |
Managed accounts |
inet:service:account |
Tenants |
inet:service:tenant, it:host:tenancy |
API endpoints and Web Apps |
inet:service:resource |
Container image |
it:software:image |
Virtual machines |
it:host, it:software:image |
Storage buckets |
inet:service:bucket |
Permissions |
inet:service:permission |
Serverless functions |
inet:service:agent, inet:service:resource |
Repositories |
it:dev:repo |
Commits |
it:dev:repo:commit |
Tracking Cloud Service Abuse in Synapse
In this section, we draw on real-world cloud-enabled operations to demonstrate how Synapse enables analysts to structurally represent, enrich, and correlate cloud threat activity, and track how threat actors operate across cloud environments.
GitHub and Dropbox being used for Malware Staging and C2
In 2020, Zscaler published APT-31 Leverages COVID-19 Vaccine Theme and Abuses Legitimate Online Services, detailing an APT-31 spearphishing campaign that leveraged GitHub to stage malware and the Dropbox API for command and control. The campaign illustrates a broader trend of chaining together multiple cloud platforms within a single attack flow.
Representing the Activity in Synapse
The table below lists the observed APT31 (Zscaler) activity, associated artifacts and technical indicators, and the corresponding Synapse forms used to model them.
Type |
Activity/Artifacts |
Synapse Form |
|---|---|---|
Cloud |
GitHub and Dropbox use |
inet:service:platform |
Cloud |
GitHub account |
inet:service:account |
Cloud |
Dropbox OAuth token |
auth:creds |
Cloud |
Dropbox API endpoint URLs |
inet:service:resource |
Technical |
File MD5 Hashes |
hash:md5 |
Technical |
URLs |
inet:url |
The modeled data is shown in the screenshot below:
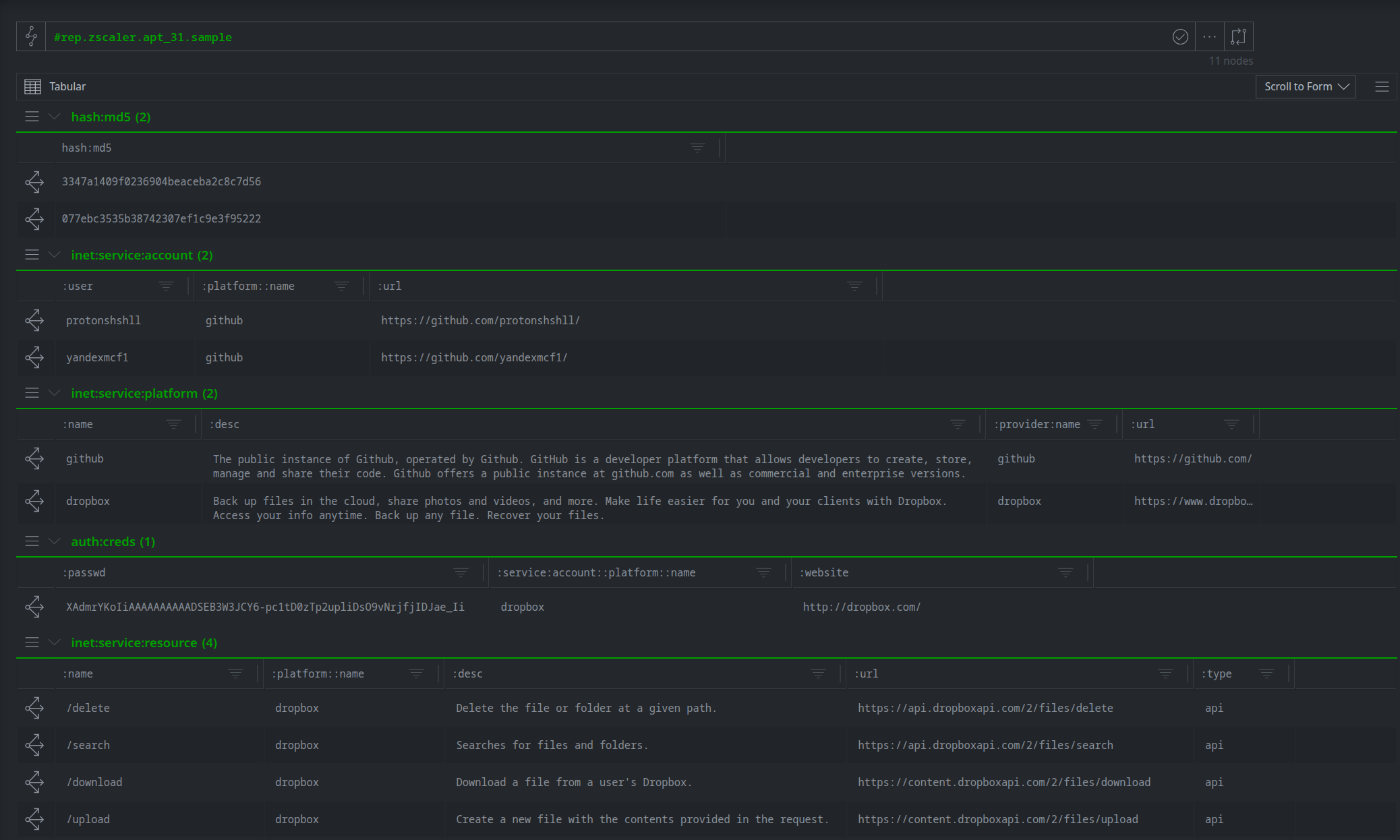
APT-31 (Zscaler) data sample
What We Can Show
With the APT-31 attack chain modeled and enriched in Synapse, we can pivot from specific IOCs to navigate the entire attack sequence, and gain a better understanding of APT-31's use of cloud platforms for malware staging.
APT-31 (Zscaler) uses GitHub to stage MSI droppers
We can navigate from the dropper’s hash to its hosting URL to reveal its staging platform.
file:bytes:md5=077ebc3535b38742307ef1c9e3f95222 -> inet:urlfile -> inet:url -> inet:fqdn -> inet:service:platform
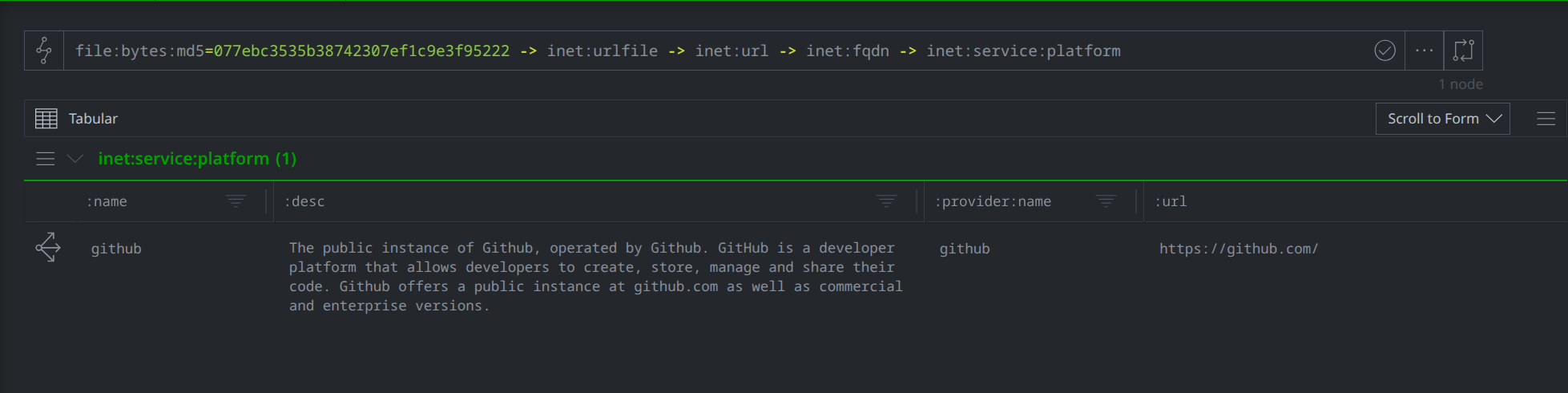
APT-31 (Zscaler) GitHub use as a staging platform
APT-31 (Zscaler) backdoors use Dropbox API endpoints for command and control
We can navigate from the dropper’s hash to the dropped payload, and show the API endpoints (resources) the payload connects to upon execution.
file:bytes:md5=077ebc3535b38742307ef1c9e3f95222 -> it:exec:file:add +:path:base=onedrive.exe :file -> file:bytes -> it:exec:url -> inet:url -> inet:service:resource
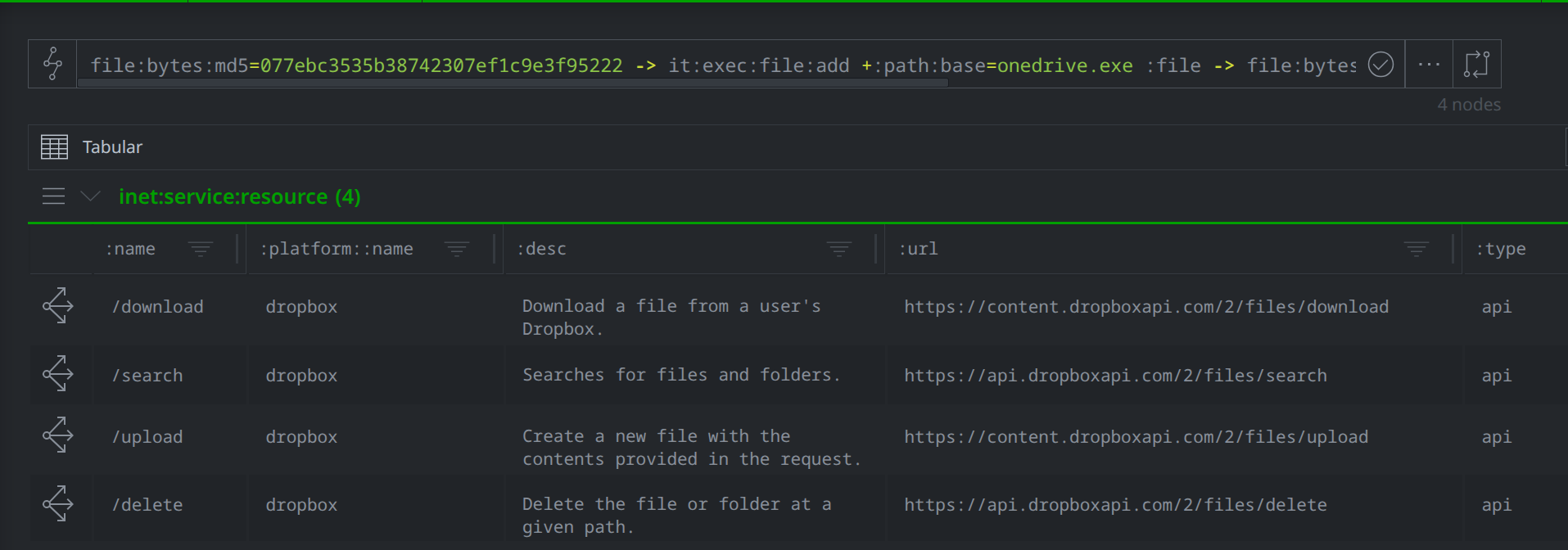
APT-31 (Zscaler) Dropbox use for C2
APT-31 (Zscaler) abuses multiple legitimate platforms within a single attack chain
Starting with a known APT-31 GitHub staging URL, we can use the tee command to show that APT-31 used GitHub and Dropbox in a single infection chain.
inet:url=https://github.com/yandexmcf1/rnicrosoft/raw/974aaa531eeb301762e486c3a120103f09a3b194/PAPER-COVID-19-Vaccine-Strategy.pdf tee {-> inet:fqdn -> inet:service:platform} {-> inet:urlfile -> file:bytes -> it:exec:file:add +:path:base=onedrive.exe :file -> file:bytes -> it:exec:url -> inet:url -> inet:service:resource -> inet:service:platform } | uniq
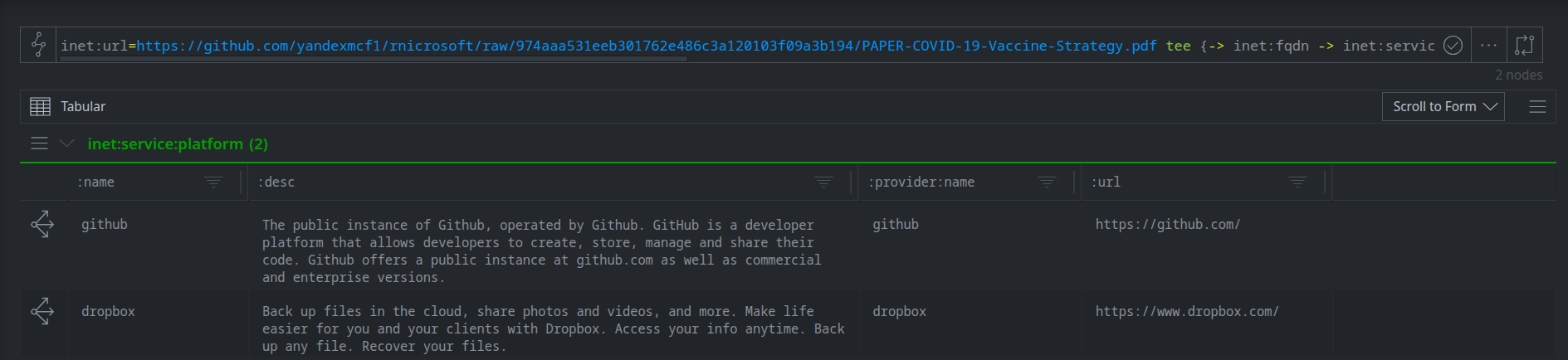
APT-31 (Zscaler) multi-platform use in a single infection chain
Tracking Backdoor Cloud Platform Evolution
In July and August 2024, Kaspersky detailed CloudSorcerer, a new APT31 cloud-based backdoor. In their report, CloudSorcerer: A New APT Threat Targeting Russian Government Organizations, Kaspersky documented the backdoor's use of GitHub, Mail.ru, Yandex, Dropbox, and Microsoft Graph as C2 channels. Shortly after public disclosure, APT31 released an updated CloudSorcerer version that uses Quora and the Russian blogging platform LiveJournal for C2, demonstrating their operational adaptability.
Representing the Activity in Synapse
The table below lists the observed APT31 (Kaspersky) activity, associated artifacts and technical indicators, and the corresponding Synapse forms used to model them. The CloudSorcerer files were not available for analysis, so the risk:* data model elements were used to capture the high-level aspects of the activity.
Type |
Activity/Artifacts |
Synapse Form |
|---|---|---|
Cloud |
Platform use |
inet:service:platform |
Cloud |
Platform accounts |
inet:service:account |
Cloud |
Account profiles |
ps:contact |
CTI |
APT31 threat actor |
risk:threat |
CTI |
CloudSorcerer software family |
risk:software:tool |
CTI |
CloudSorcerer reporting |
media:news |
Technical |
CloudSorcerer files |
The modeled data is shown in the screenshot below:
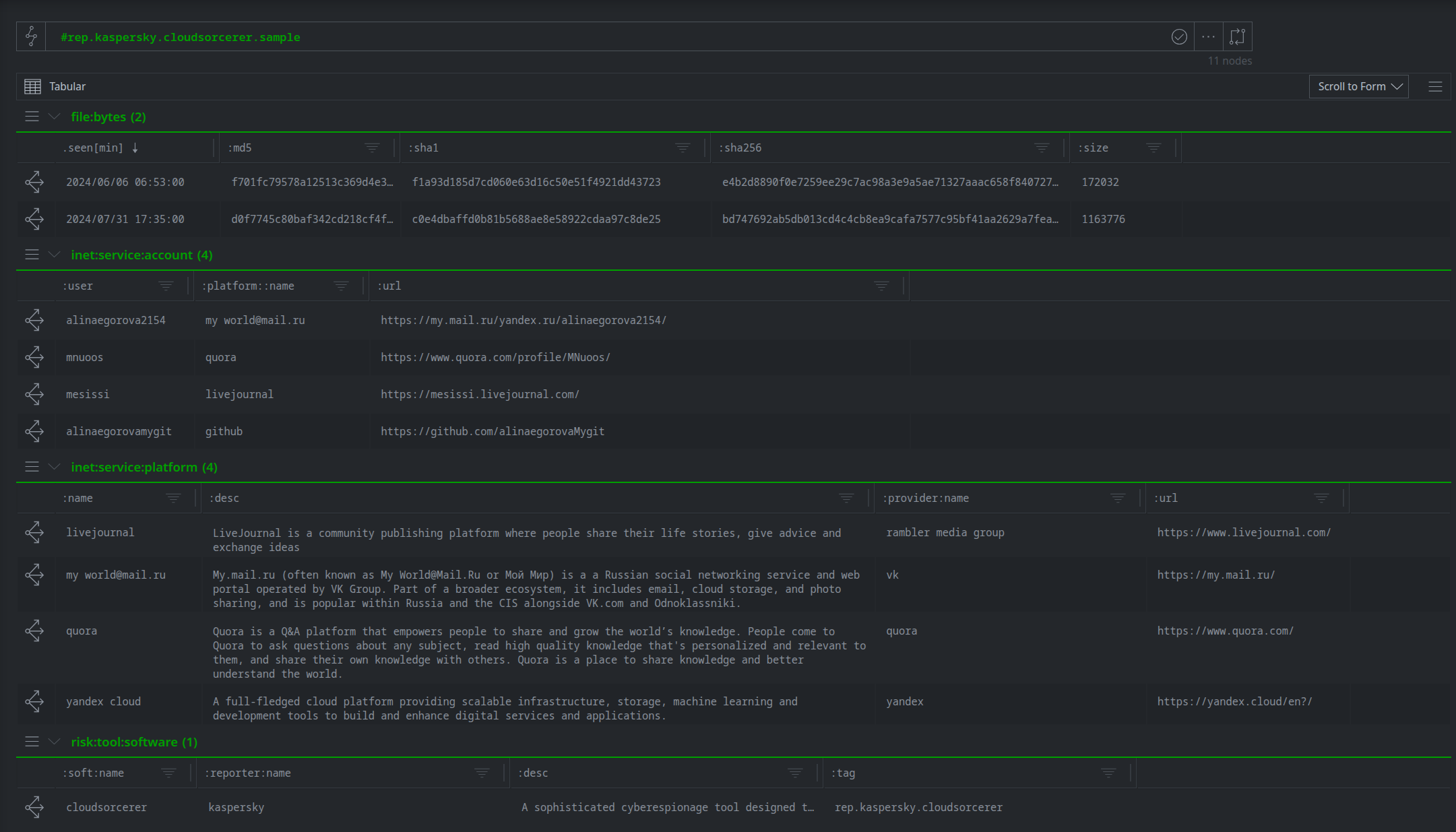
APT-31 (Kaspersky) data sample
What We Can Show
With the CloudSorcerer (Kaspersky) activity added to Synapse, we can pivot through the graph to show CloudSorcerer’s use of cloud account profiles for C2 across multiple platforms, and their ability to rapidly respond to public disclosure.
CloudSorcerer (Kaspersky) has leveraged 7 cloud platforms for C2
We can walk from the CloudSorcerer software family to the platforms it has been observed using.
risk:tool:software:soft:name=cloudsorcerer -(uses)> inet:service:platform
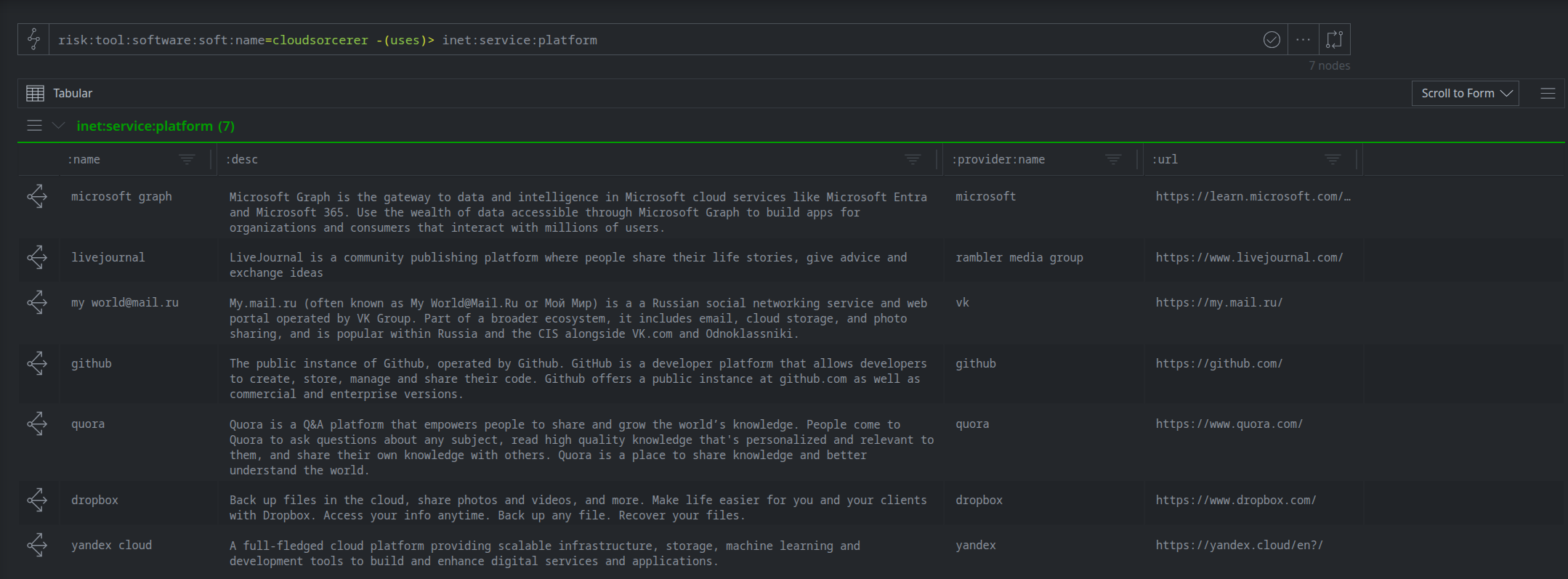
APT-31 (Kaspersky) platform use
CloudSorcerer (Kaspersky) uses photo captions and account profiles as C2 dead drop resolvers
We can lift the cloud accounts tagged with #rep.kaspersky.cloudsorcerer and pivot to the linked message and contact nodes to view the C2 data stored in My World photo captions and account profiles across various platforms.
inet:service:account#rep.kaspersky.cloudsorcerer tee { -> inet:service:message } { -> ps:contact +:bio } | uniq
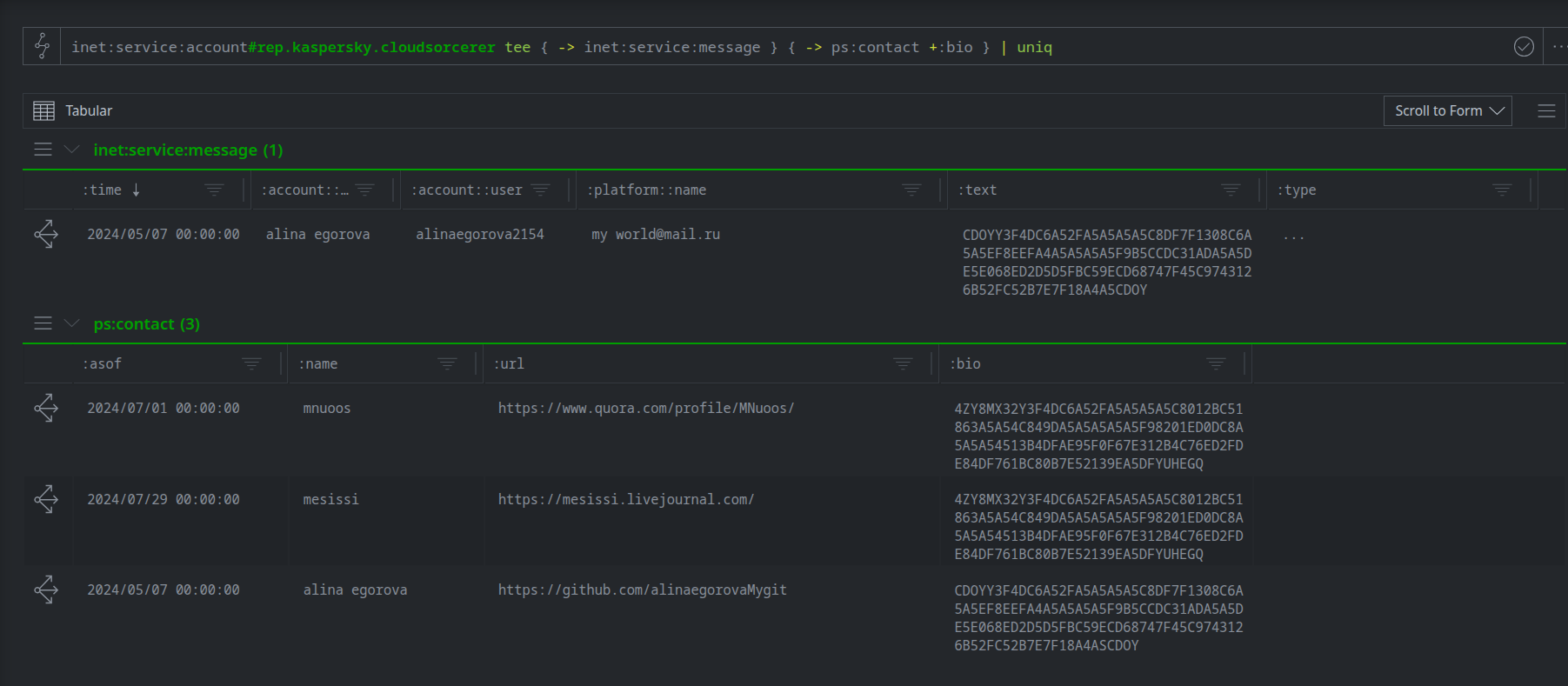
CloudSorcerer (Kaspersky) C2 data in messages and account bios
APT31 (Kaspersky) updated CloudSorcerer’s C2 platform less than 1 month following public disclosure
We can walk from the CloudSorcerer public reports to the referenced CloudSorcerer files and accounts.
media:news:topics*[~=cloudsorcerer] -(refs)+> (file:bytes,inet:service:account)
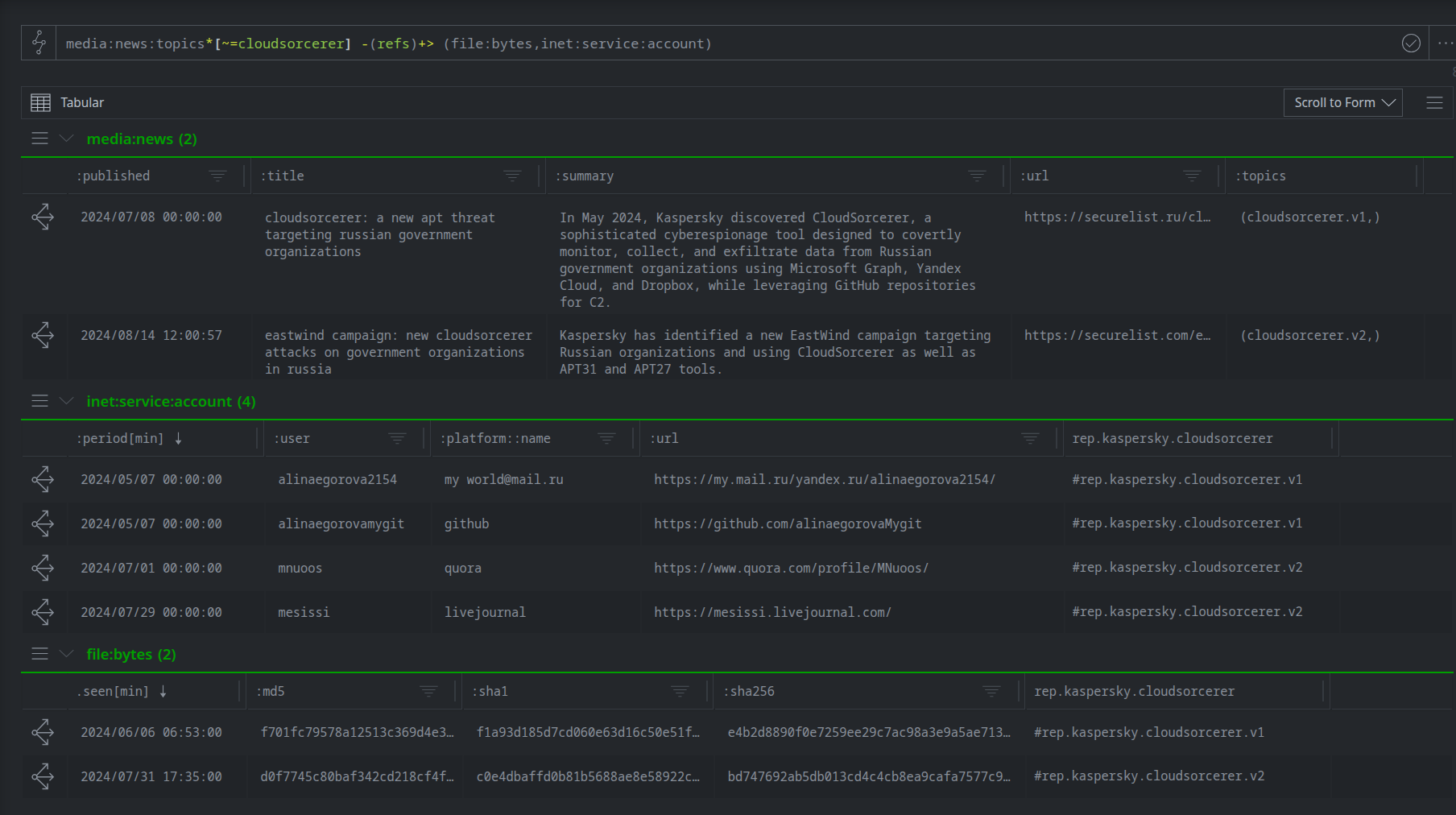
CloudSorcerer (Kaspersky) reports and C2 accounts
Actor-Provisioned Azure Infrastructure for C2
In 2024, Microsoft published Peach Sandstorm deploys new custom Tickler malware in long-running intelligence gathering operations, documenting the Iranian threat actor's use of the Microsoft Azure App Service platform to facilitate CNO. Peach Sandstorm provisioned resources within actor-controlled Azure subscriptions, leveraging Azure subdomains (*.azurewebsites.net) for Tickler malware C2.
Representing the Activity in Synapse
The table below lists the observed Peach Sandstorm (Microsoft) activity, associated artifacts and technical indicators, and the corresponding Synapse forms used to model them.
Type |
Activity/Artifacts |
Synapse Form |
|---|---|---|
Cloud |
Azure use |
inet:service:platform |
Cloud |
Azure App Service use |
inet:service:platform |
Cloud |
Tickler Azure C2 infrastructure |
inet:service:resource |
Technical |
Domain names |
inet:fqdn |
Technical |
File SHA256 hashes |
hash:sha256 |
The modeled data is shown in the screenshot below:
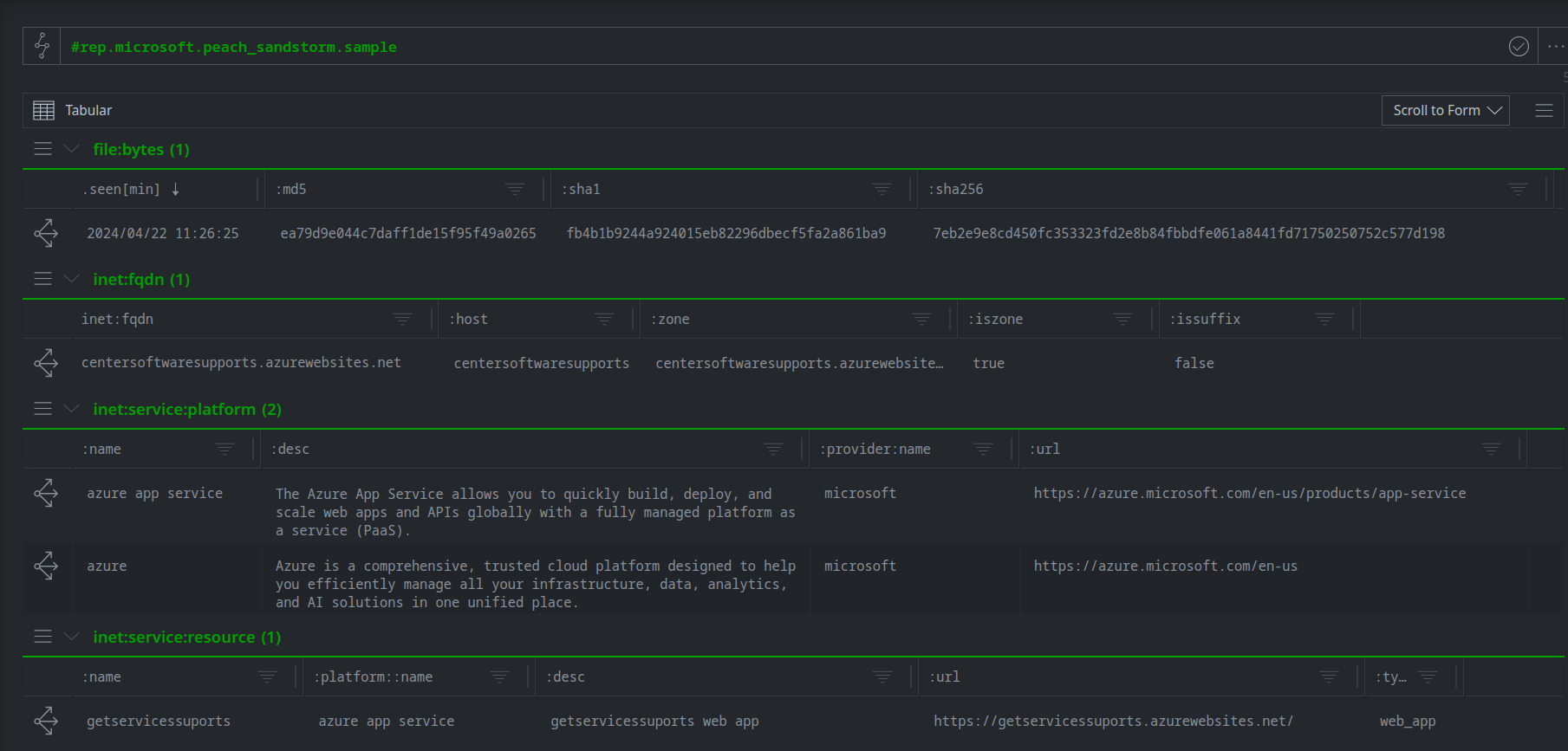
Peach Sandstorm (Microsoft) data sample
What We Can Show
With the Peach Sandstorm (Microsoft) Tickler hashes and Azure abuse activity modeled and enriched in Synapse, we can pivot through the graph to show their Azure Web App use.
The Tickler (Microsoft) backdoor uses the Microsoft Azure App Service as a C2 platform
We can navigate from a Tickler sample to its DNS request and show the resolved domain belongs to the Azure App Service zone (azurewebsites.net).**
file:bytes#rep.microsoft.peach_sandstorm -> inet:dns:request -> inet:fqdn :domain -> inet:service:platform:zone | uniq
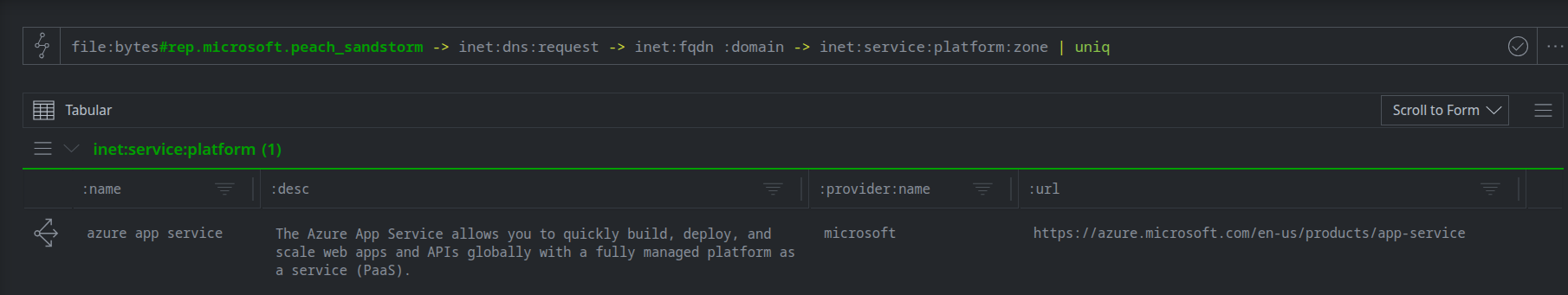
Tickler (Microsoft) Azure App Service use
Peach Sandstorm (Microsoft) provisions multiple Azure resources to facilitate CNO
We can navigate from known Peach Sandstorm (Microsoft) infrastructure to the Azure Web App provisioned by the actor.
inet:fqdn#rep.microsoft.peach_sandstorm -> inet:url -> inet:service:resource
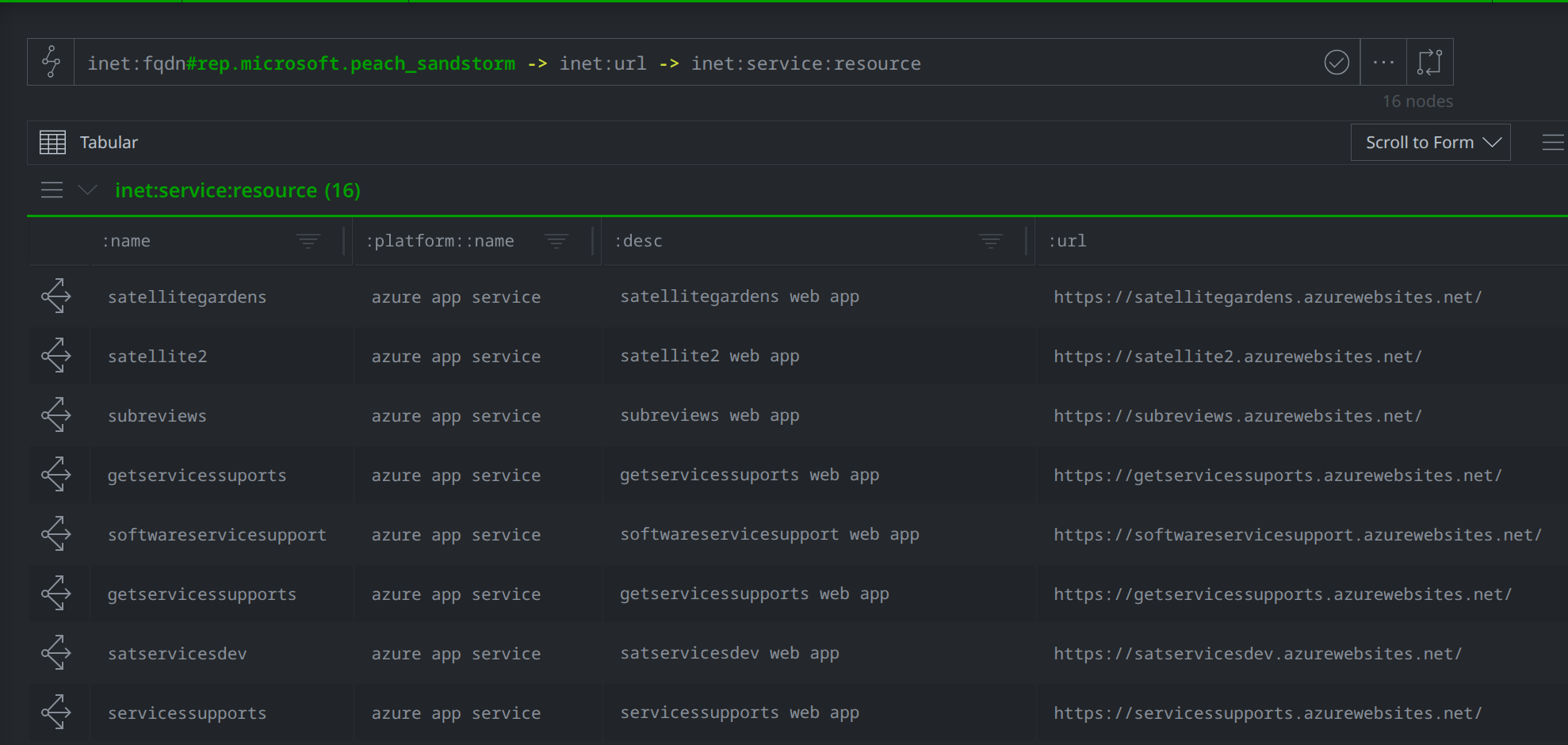
Peach Sandstorm (Microsoft) Azure resource use
VirusTotal Comments as a Dead Drop Resolver
In late 2025, Positive Technologies published Attacks of the Striking Panda: APT31 Today, detailing APT31’s VtChatter malware. VtChatter uses APT31-controlled accounts to post encoded C2 data as comments on files via the VirusTotal Files API endpoint.
Representing the Activity in Synapse
The table below lists the observed VtChatter (Positive Technologies) activity, associated artifacts and technical indicators, and the corresponding Synapse forms used to model them.
Type |
Activity/Artifacts |
Synapse Form |
|---|---|---|
Cloud |
VirusTotal platform use |
inet:service:platform |
Cloud |
VirusTotal account |
inet:service:account |
Cloud |
VirusTotal comments |
inet:service:message |
Technical |
File SHA256 hash |
hash:sha256 |
Technical |
RC4 key |
crypto:key |
The modeled data is shown in the screenshot below:
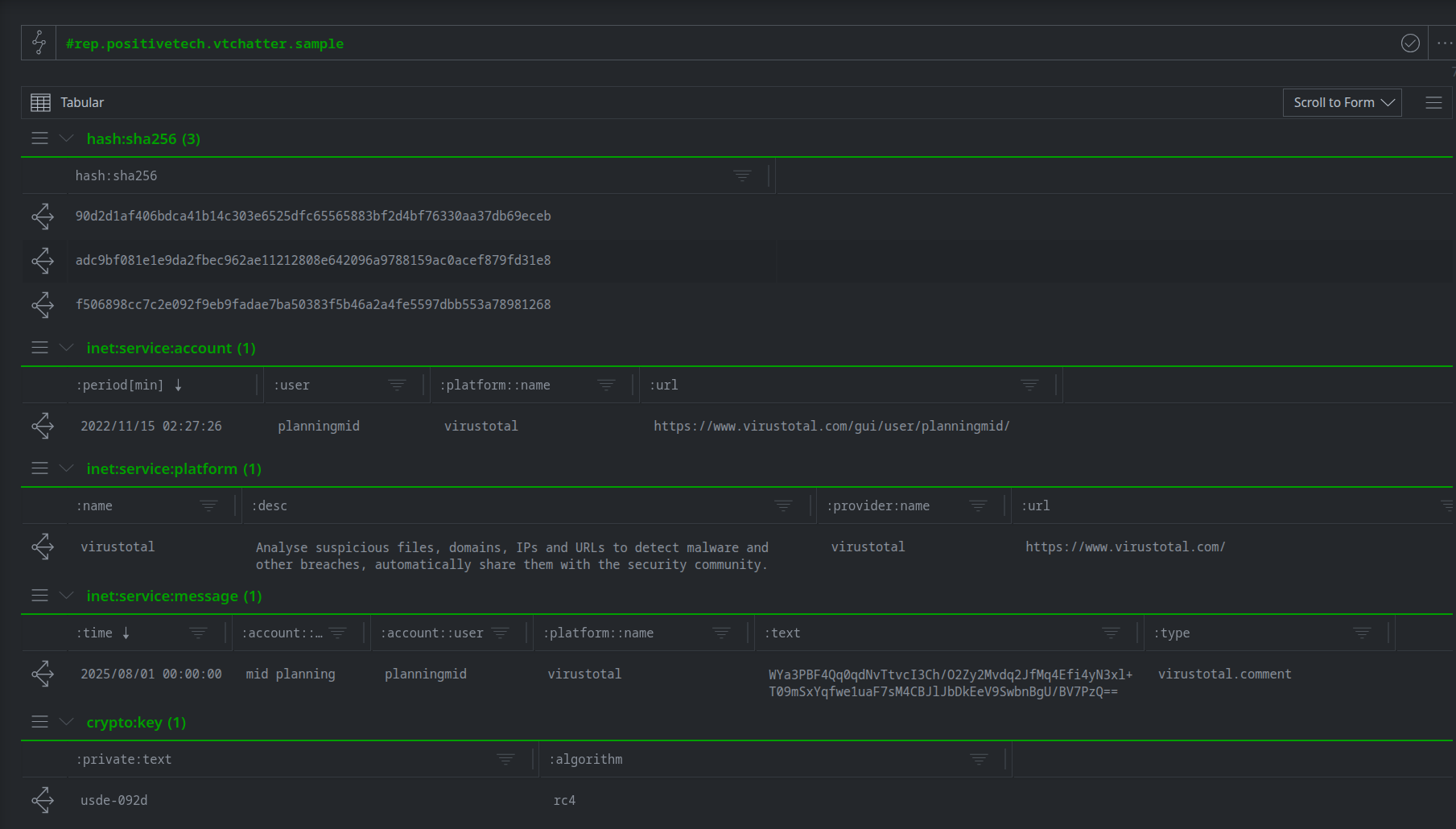
VtChatter (Positive Technologies) data sample
What We Can Show
With the APT31 (Positive Technologies) VirusTotal activity added and enriched in Synapse, we can pivot through the graph to show VtChatter C2 configuration data.
APT31 (Positive Technologies) created a VirusTotal account in November 2022
We can pivot from the VirusTotal platform to the known APT31 registered VirusTotal account.
inet:service:platform:name=virustotal -> inet:service:account +#rep.positivetech.vtchatter
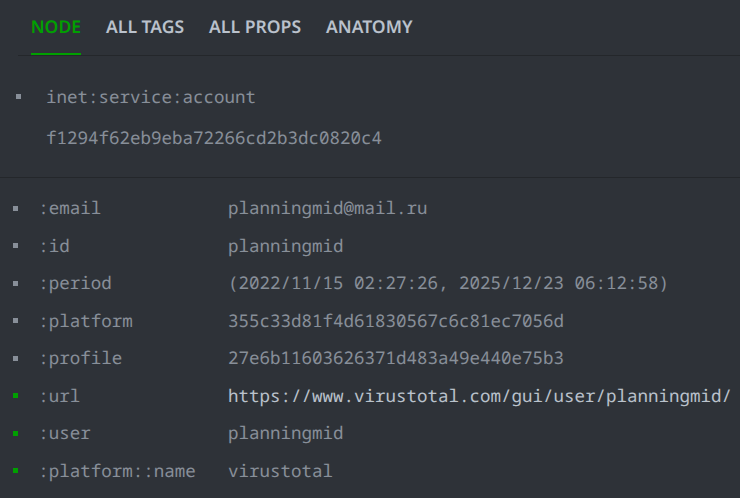
APT31 (Positive Technologies) Virustotal account
APT31 (Positive Technologies) uses their registered VirusTotal account to post base64 encoded messages in VirusTotal comments
We can pivot from the APT31 VirusTotal account to the posted VirusTotal comments.
inet:service:account:user=planningmid -> inet:service:message
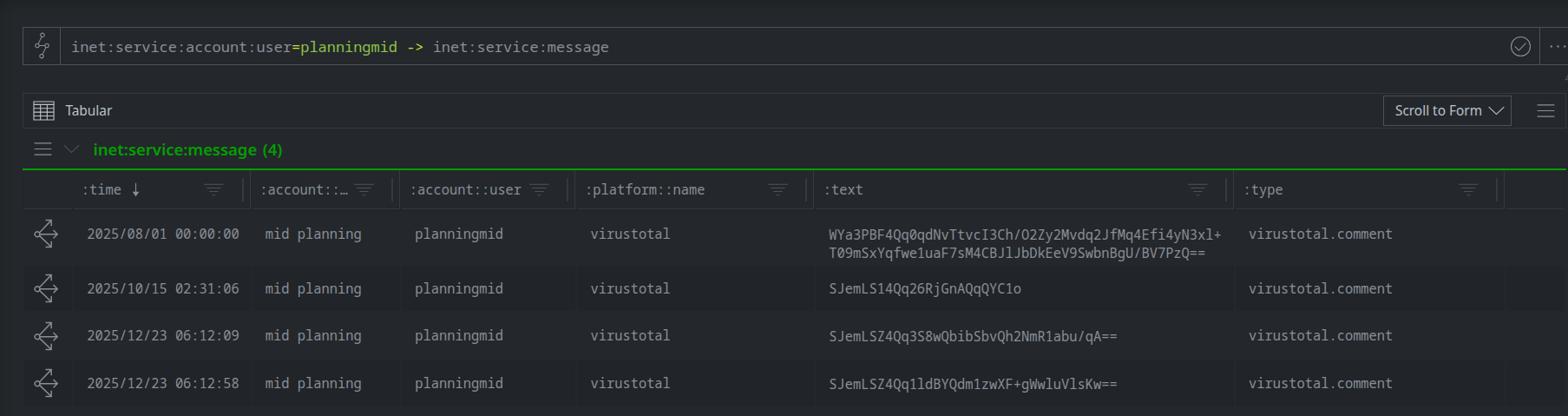
APT31 (Positive Technologies) Virustotal comments
VtChatter VirusTotal comments contain encoded and encrypted commands and command output
We can pivot from the APT31 VirusTotal account to the base64 decoded and RC4 decrypted VirusTotal comments output. Using path variables we can display the comment alongside the decrypted output.
inet:service:account:user=planningmid -> inet:service:message $comment=:text -(refs)> it:dev:str -(refs)> * $path.meta.comment = $comment

APT31 (Positive Technologies) using VirusTotal for C2
Summary
Cloud environments are now central to modern computer network operations. Threat actors are abusing the same platforms organizations rely on for business operations to conduct reconnaissance, establish footholds, exfiltrate data, and control implants. Cloud accounts, code repositories, and tenants are now the default artifacts of threat activity, and CTI telemetry and workflows must reflect this reality.
Synapse’s expanded data model elements allow analysts to structurally represent cloud artifacts as first-class entities alongside traditional observables. This gives analysts the flexibility to pivot from a malware sample to its cloud staging platform, trace C2 activity through API endpoints and account profiles, capture how threat actors chain multiple cloud services within a single attack flow, and track how a malware family evolves its cloud infrastructure over time. The result is a modernized CTI workflow with complete visibility across both cloud and traditional environments, and the ability to accurately characterize, correlate, and respond to modern CNO.
