Now You See Me: Tracking DDoSia’s Rapidly Changing Infrastructure with the Synapse-Censys Power-Up
by savage | 2026-02-25
The Vertex Project and Censys recently hosted a joint webinar highlighting the Synapse-Censys Power-Up and how analysts can use it to query Censys’ data and represent their findings within Synapse. For our use case, we focused on how an analyst might use the Synapse-Censys Power-Up to research infrastructure associated with a group called NoName057(16) and its use of a custom Distributed Denial of Service toolkit known as DDoSia. This blog will walk through several of the webinar’s key points.
What is the Synapse-Censys Power-Up?
Power-ups are Storm packages and services that can connect to an external data source for integration with Synapse and provide additional functionality to Synapse. The Synapse-Censys Power-Up serves as a connector between Synapse and Censys’ Platform API. With the Synapse-Censys Power-Up, analysts can use Storm commands or node actions to query Censys’ holdings for current and historical host and certificate data and then represent those findings in Synapse.
The Synapse-Censys Power-Up is one of many Rapid Power-Ups that The Vertex Project has developed. While we regularly add new Power-Ups to Synapse, you can view those that are currently available on this list. Customers can also develop and implement their own.
The Use Case: NoName057(16) and DDoSia
To demonstrate how an analyst might use the Synapse-Censys Power-Up for their research, we focused on a group that calls itself NoName057(16) and manages a Distributed Denial of Service (DDoS) toolkit called DDoSia.
Note
The data used during this webinar is available for review in the "TLP:White" view within the Vertex Intel-Sharing Synapse Instance (the "VISI", for short). You can request access to the VISI here.
Once you have access to the VISI, you’ll be able to view a short primer we’ve created on NoName057(16) titled "NoName057(16) & DDoSia Primer". You’ll also be able to view the data we’ve used for this webinar, which is located in the "TLP: Clear" view and tagged with #vtx.story.ddosia.
In a December 2025 blog post, Censys discussed the challenges involved in identifying and tracking NoName057(16) and DDoSia activity due to the group’s “minimal footprint” and rapid infrastructure rotation. With this in mind, an analyst could use the Synapse-Censys Power-Up to enrich the group’s previously identified infrastructure with details and context from Censys’ holdings, and then review that data for insights that can inform queries hunting for new infrastructure.
Using the Synapse-Censys Power-Up to Enrich Known Infrastructure
As part of our initial research into DDoSia activity, we modeled Censys’ December 2025 blog and reported indicators, including the IP addresses listed on Github. The easiest way to query the Synapse-Censys Power-Up for any additional information about these IP addresses is to use the available node action accessible through the Context Menu. The Power-Up documentation identifies any node actions automatically installed alongside the Power-Up, and notes which forms that each is able to operate on. In the case of these IP addresses (inet:ipv4 nodes), we are able to use the platform.hosts.enrich node action to query Censys for information about one or more of the IP addresses.
In the image below, we’ve selected all inet:ipv4 nodes, right-clicked to access the Context Menu, and navigated to the Synapse-Censys node actions to run platform.hosts.enrich:
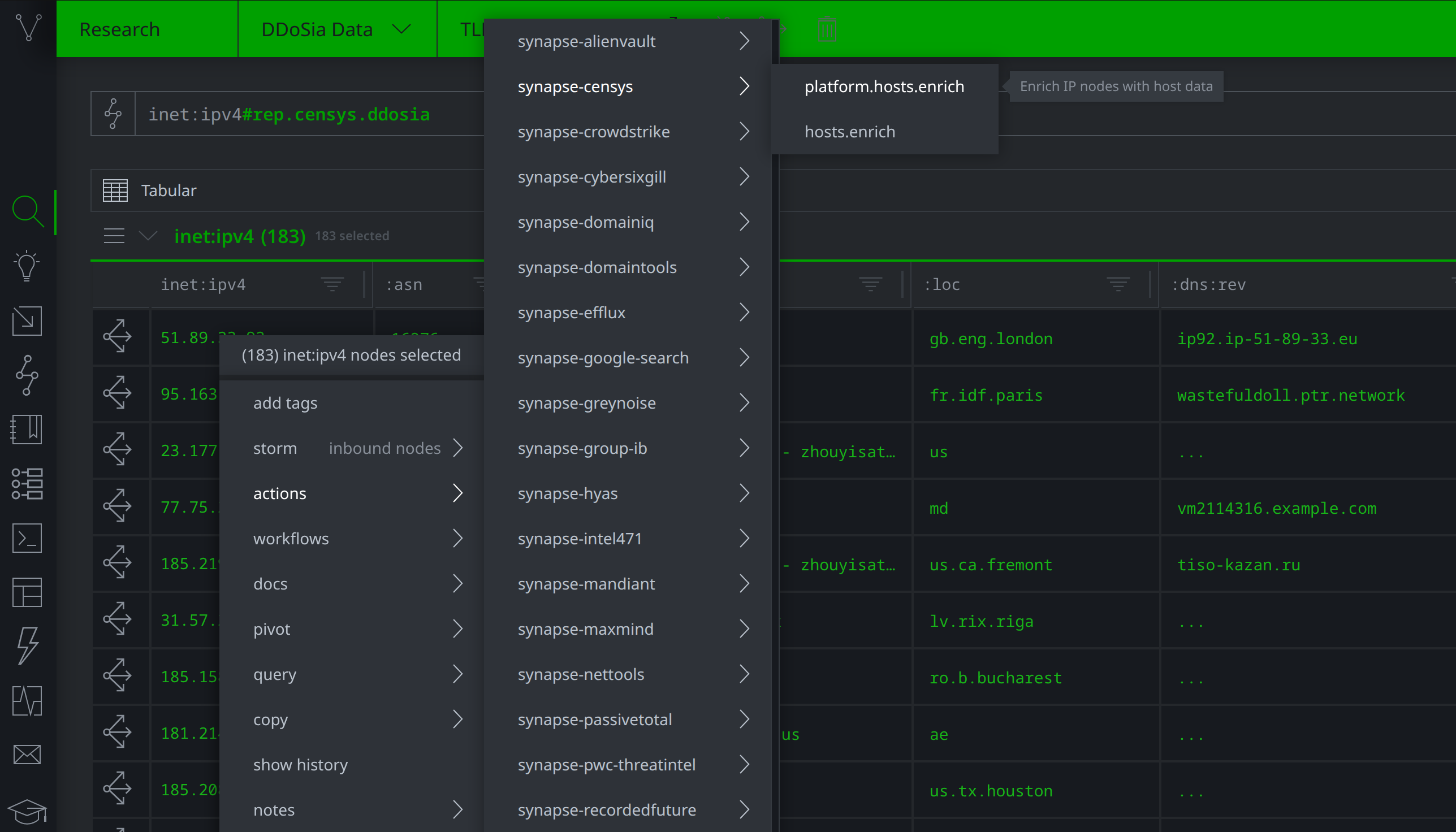
Selecting the platform.hosts.enrich node action to query the Synapse-Censys Power-Up
Once the query is complete, we can review the returned data. In the image below, we’ve selected one of the inet:ipv4 nodes to review, and clicked the Explore button beside the node to view related information mapped to the node in the graph. New nodes and tags are underlined because we have Review Mode selected in our Cortex.
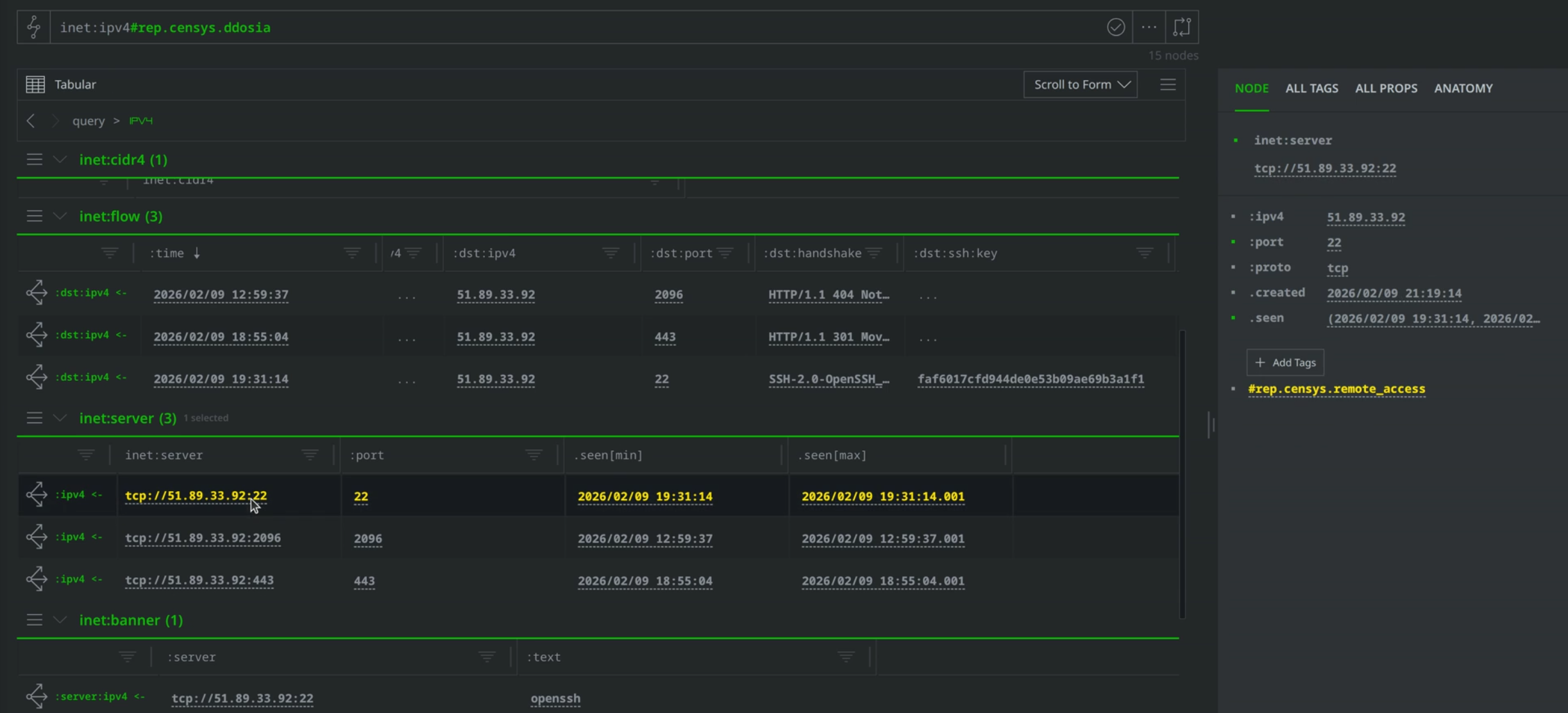
Reviewing new data brought into Synapse through the Synapse-Censys Power-Up
Some of the information returned includes inet:flow and inet:server nodes. One of the inet:server nodes has a #rep.censys.remote_access tag, indicating that Censys reports that the server is associated with remote access activity.
While node actions are a quick and easy way to query a Power-Up, analysts can also use the Power-Up’s associated Storm commands for more flexible query options. In the query below, we use the Synapse-Censys Power-Up’s censys.platform.hosts.history command to query Censys for historical data about the IP addresses. Our query uses the --period flag to specify that we are interested in data between July 17, 2025 and the current date:
inet:ipv4#rep.censys.ddosia censys.platform.hosts.history --period (20250717, now)
After the query runs, we can again use the Explore button to navigate out from one or more selected inet:ipv4 addresses to view the returned data.
Searching for New Infrastructure with the Synapse-Censys Power-Up
In addition to using the Synapse-Censys Power-Up to query Censys for more details about known infrastructure, we can also use the Power-Up to hunt for new or previously unidentified infrastructure using the censys.platform.search command. This is the Power-Up’s most flexible query option, which analysts can pair with the Censys Query Language to search Censys’ holdings. For our use case, we would ideally use this command to hunt for new DDoSia infrastructure by crafting a query that searches for a combination of qualities we’ve observed in DDoSia’s previous infrastructure.
Although Censys’ blog on DDoSia noted the difficulties in identifying and tracking related infrastructure, we can still look for some trends and commonalities in previously reported infrastructure to help serve as a guide. The query below, for example, lifts all IP addresses Censys attributed to NoName057(16) and DDoSia activity, pivots to the inet:asn nodes representing the associated Autonomous System (AS) Numbers (ASN), then filters to display those with more than 6 associated DDoSia servers:
inet:ipv4#rep.censys.ddosia -> inet:asn +{-> inet:ipv4 +#rep.censys.ddosia}>6
Running this query in Statistics mode will display the names of the most frequently used AS networks among the infrastructure reported in Censys’ blog, as seen below:
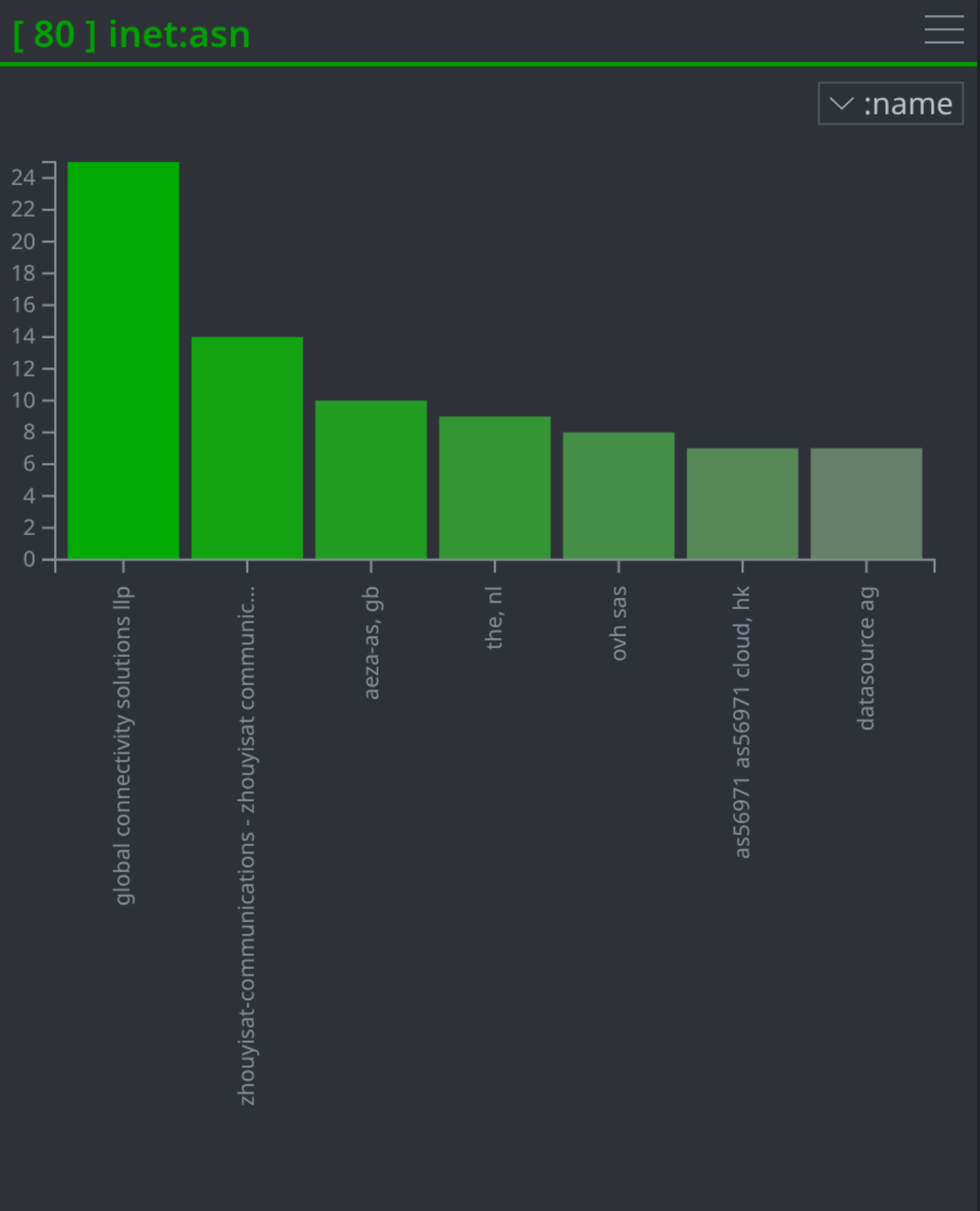
Statistical breakdown of the most frequently used AS networks found in the query results
Once we’ve identified a combination of criteria to look for, we can use the censys.platform.search command to query Censys’ holdings for unreported DDoSia infrastructure. If we happen to develop a query that is particularly successful, we might consider automating it as a Cron job. Anything written in Storm can be automated, and scheduling the query to run regularly and search for new DDoSia infrastructure would free an analyst from having to remember to run the query manually.
Analysts might also consider creating a Trigger to enrich reported DDoSia infrastructure with Censys data. The following image displays a trigger designed to fire whenever a "rep" (for "reported") tag with "DDoSia" as the base is applied to an inet:ipv4 node. The trigger will run both the censys.platform.hosts.enrich and censys.platform.host.history commands, pulling in additional context from Censys along with host history from the past thirty days.
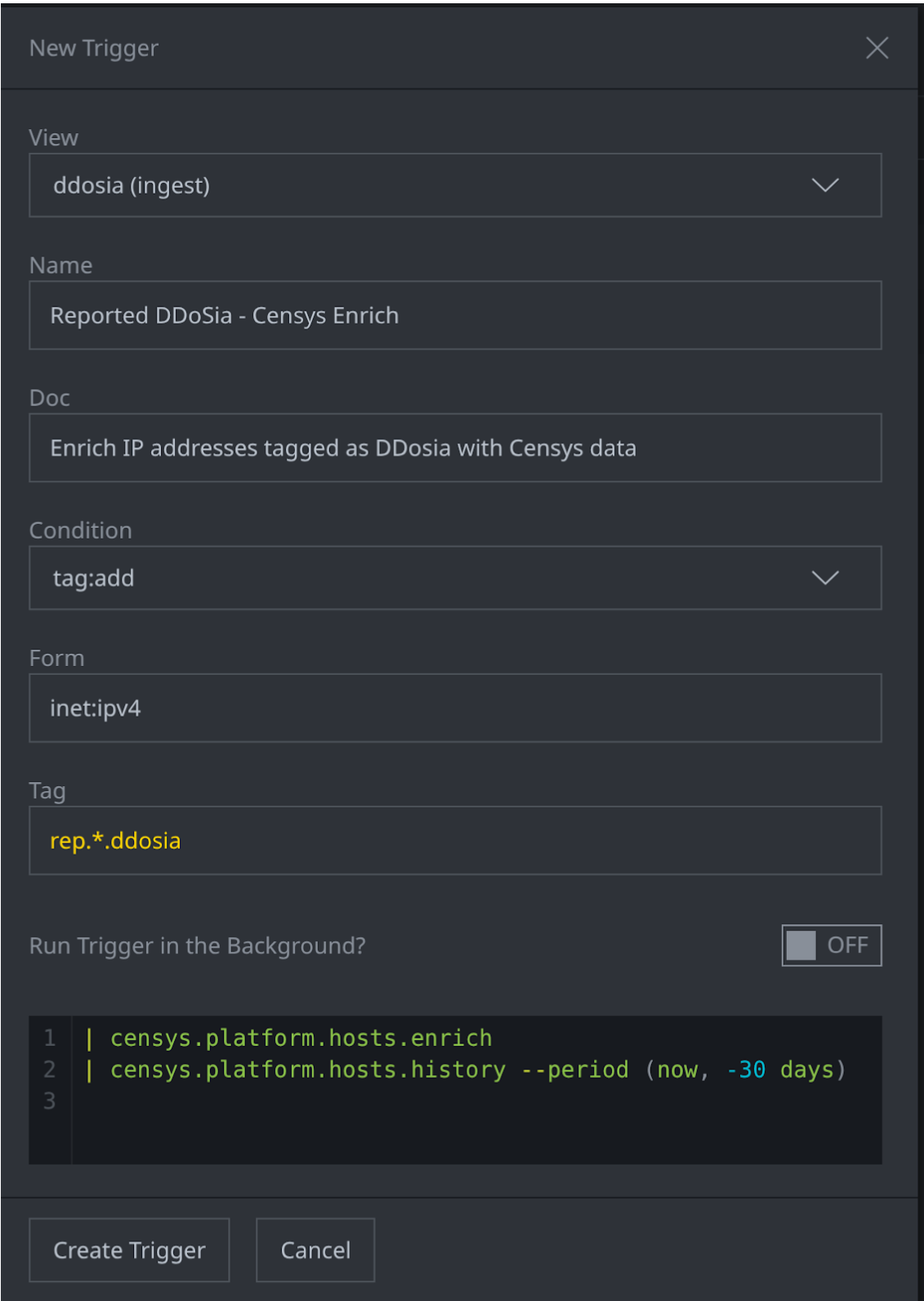
Trigger written to query Synapse-Censys Power-Up to enrich IPs tagged as associated with DDoSia
Bringing Censys' Visibility Into Synapse
The Synapse-Censys Power-Up is one of the many Rapid Power-Ups that analysts working in Synapse can use to connect to external data sources for use in research and analysis. Analysts can use the Synapse-Censys Power-Up in particular to query Censys’ data and monitor their own company’s exposures or those of supply chain partners, as well as identify and track threat actor infrastructure. You can learn more about Censys through the website.
Interested in trying out Synapse yourself? Request your own Synapse demo instance! For more news and updates, follow The Vertex Project on Bluesky and join the Synapse community Slack.
